Red Teaming
Red Teaming is a comprehensive security assessment where ethical hackers simulate real-world attackers’ Tactics, Techniques, and Procedures (TTPs) on all aspects of an organization, including its people, processes, and technology infrastructure. Unlike traditional vulnerability scanning or penetration testing, which focuses on specific vulnerabilities, Red Teaming takes a holistic yet objective-based approach, providing organizations with a more accurate assessment of their security posture.
The Red Team comprises highly skilled security professionals who take on the role of attackers to assess the effectiveness of an organization’s defensive measures. They aim to uncover potential security gaps, demonstrating how attackers combine unrelated exploits to access sensitive data and critical assets. Following the assessment, the team provides recommendations and plans to bolster the organization’s security posture, ensuring it remains resilient in the face of evolving threats.
What Is Continuous Red Teaming?
Continuous Red Teaming is a proactive and dynamic offense strategy that establishes a continuous cycle of testing, learning, fixing, and evolving tactics to create a resilient security framework that effectively identifies and addresses vulnerabilities. It involves regular testing of the environment by emulating different potential threat actors, thus pursuing diverse threat objectives every time. This approach of employing different TTPs in each test ensures a comprehensive evaluation of defense mechanisms against existing as well as emerging threats.
These assessments help assess the preparedness of internal teams to handle incidents, fostering an adaptive cybersecurity approach. Typically performed in a “low and slow” manner with custom tools and scripts that are not easy to detect, these assessments avoid triggering alerts easily, making them more expensive than regular penetration tests.
Furthermore, Continuous Red Teaming assessments will also aid in answering the following questions:
- Can we determine if a persistent and skilled attacker can achieve the flag using the TTPs?
- Do internal detection and reporting capabilities meet the required standards?
- Have we adequately assessed the effectiveness of our Incident Response practices and Blue Team capabilities?
- Have internal teams and external service providers fulfilled their Service Level Agreements (SLAs)?
Importance of Red Team Assessment
-
Effective Risk Assessment: According to recent statistics, 47% of organizations believe red teaming is a best practice for risk assessment. This approach helps them uncover unknown vulnerabilities and weaknesses in their security measures, which is crucial for protecting their valuable assets and sensitive information.
-
Data Protection: Red team assessment evaluates how well data protection measures work, especially for sensitive information like personally identifiable information (PII) and intellectual property (IP). This ensures that critical data remains safe from potential threats.
-
Real-World Simulation: Red teaming simulates real-world attack tactics, techniques, and procedures (TTPs) that actual threat actors might use. This helps organizations prepare for and defend against realistic threats rather than hypothetical scenarios.
-
Strengthening Security Defenses: By leveraging insights into the latest attack methods and vectors, red team assessment aims to expose vulnerabilities in security defenses. This proactive approach helps organizations strengthen security measures to protect against evolving threats.
-
Identification of Vulnerabilities: Red team assessment identifies known and unknown vulnerabilities, along with misconfigurations in applications and network infrastructure. This ensures that potential weaknesses are promptly addressed to reduce the risk of exploitation.
-
Performing Reconnaissance Activities: Conducting reconnaissance activities to assess the security of unprotected system data helps organizations identify information that could be valuable to potential attackers and take appropriate measures to prevent security breaches.
Why Choose Accorian?
Accorian is a leading cybersecurity firm, distinguished by its CREST accreditation, renowned for unparalleled expertise. Our team comprises technology and cybersecurity leaders, ensuring proficiency that exceeds industry standards. What truly distinguishes us is our commitment to tailor-made solutions. Each red team assessment, backed by our remarkable 100% success rate, is meticulously customized to meet an organization’s unique needs, ensuring relevance and effectiveness in today’s business landscape.
Red Team Methodology
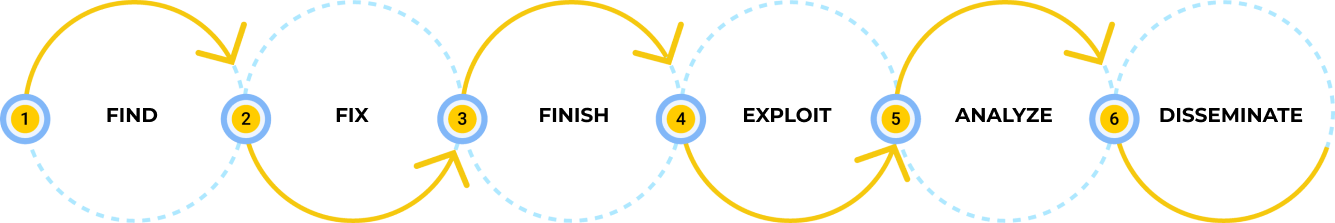
Accorian utilizes the F3EAD methodology integrated with the MITRE ATTACK framework, employing a systematic approach consisting of distinct phases:
Fix
In the Fix phase, the focus involves intense reconnaissance and intelligence collection against the selected target, delving into the intricacies of the target’s systems, networks, and potential points of exploitation. This step is vital in the Red Team assessment process, aiming to attain a level of familiarity with the target that facilitates informed decision-making in subsequent phases of the F3EAD methodology.


Finish
In the Finish phase, the focus shifts to setting plans into action by deploying Tactics, Techniques, and Procedures (TTPs) in a decisive and coordinated manner. This phase integrates various elements, including toolsets, intelligence, capabilities, and human expertise, amalgamating into a comprehensive and potent weapon system. It’s the focal point where planning and reconnaissance transition into practical, impactful actions. MITRE ATTACK TTPS are pivotal in shaping the attack path and enhancing the red team’s ability to navigate and exploit vulnerabilities effectively.
Exploit
In the exploitation phase, Accorian acts as the Red Team actor and operationalizes the detailed attack plan into action to achieve mission objectives. This phase represents the culmination of strategic planning and the initiation of exploits to realize Red Team objectives.


Analyze
In the analysis phase, the team gains insights into the systems’ responses; they can adjust their tactics and techniques accordingly. This phase involves continuous updates, revisions, and modifications to the attack path and exploitation strategies. Whether an exploit succeeds or fails, the iterative nature of the phase ensures that our testers remain agile and responsive to evolving conditions.
Disseminate
In the dissemination phase, raw assessment data is transformed into actionable intelligence, acting as a vital link between the Red Team’s activities and the broader organizational context. This documentation provides:
- A comprehensive record of the assessment’s results
- Guides organizations with the next steps, empowering leadership for strategic decision-making
- Fortifies the overall security posture

Attack Scenario Examples
COMPROMISE OF
ACTIVE DIRECTORY
Activity: Conduct a targeted cyberattack against employees to gain unauthorized access to their computer systems. Proceed to perform lateral movement within the organization’s network and identify domain or enterprise administrators, aiming to compromise their accounts.
Objective
Evaluate the organization’s defenses concerning Active Directory (AD) security.
Assess the capability of the security team to detect and respond to a multi-stage cyberattack.
Demonstrate the effectiveness of the organization’s incident response procedures.
Attack Vector: Internal
C-LEVEL EXECUTIVE
EMAIL ACCESS
Activity: Simulate a phishing campaign to compromise the email accounts of C-level executives. Additionally, crawl the dark web to acquire compromised credentials.
Objective
Assess the effectiveness of cybersecurity awareness training provided to employees, particularly regarding phishing attacks.
Investigate the presence of the organization’s data on the dark web.
Evaluate the capability of the security team to detect and respond to a multi-stage cyberattack, starting with a phishing attempt.
Attack Vector: External
EXFILTRATION OF
SENSITIVE DATA
Activity: Conduct a cyberattack to gain unauthorized access to sensitive data and exfiltrate information covertly.
Objective
Assess the ability of the security team to detect a multistage cyberattack.
Determine the extent to which a persistent attacker could compromise confidential information.
Prove the effectiveness of incident response procedures.
Attack Vector: Internal/External
BACKDOORING APPLICATION ON
PRODUCTION/ STAGING
Activity: Install a backdoor that will provide an attacker with continued access to the system or other application resources.
Objective
Evaluate the security team’s capability to identify and respond to a multi-stage cyberattack involving backdooring.
Demonstrate the effectiveness of the organization’s incident response procedures in detecting and mitigating threats involving backdoors.
Attack Vector: Internal
GAINING ACCESS TO
SECURE CODE
Activity: Execute a cyberattack to gain unauthorized access to the source code of applications and covertly exfiltrate this information.
Objective
Assess the security team’s capacity to detect and respond to a multi-stage cyberattack targeting source code.
Determine how much a persistent attacker could compromise confidential information through source code access.
Demonstrate the effectiveness of the organization’s incident response procedures in detecting and mitigating source code breaches.
Attack Vector: Internal
Key Differentiators
Accorian is a leading cybersecurity and compliance firm with a wealth of experience to help navigate organizations on their information security journey. Our services, including HITRUST, HIPAA, PCI, ISO, NIST, Incident Response, Risk Assessment, Penetration Testing, vCISO, and Red Teaming, reflect our commitment to providing comprehensive solutions tailored to specific regulatory needs. With our distinctive, hands-on, white-glove approach and goal-oriented, proven methodology, we ensure compliance and deliver tangible fiscal value and unparalleled expertise to our clients.
Our test plans aim to cover 200-400 checks for network penetration tests and 400-800 reviews for application penetration tests
Our time-tested and proven penetration testing methodology is built using OSSTMM, OWASP, NIST, and PTES standards
End-to-end project management for assessments with comprehensive and detailed reporting through our platform
We leverage our automated scanners and tools along with our custom scripts to conduct thorough assessments and ensure comprehensive coverage
Combined experience of working with 500+ clients on 1200+ penetration tests, detection of 25000+ vulnerabilities, and 100% success rate in red team engagements
A Trusted Vulnerability Assessor and an
Approved Scan Vendor (ASV) for organizations in sectors such as banking, financial services, credit unions, eCommerce, and SaaS that need to adhere to PCI DSS requirements
CONSULTING & ASSESSMENT SERVICES
Office Address
Accorian Head Office
6,Alvin Ct, East Brunswick, NJ 08816 USA
Accorian Canada
Toronto
Accorian India
Ground Floor,11, Brigade Terraces, Cambridge Rd, Halasuru, Udani Layout, Bengaluru, Karnataka 560008, India
Ready to Start?
Wordpress Developer (3-5 Years)
Senior Manager - Penetration Testing (5-7 years)
Senior Manager - Compliance (5-7 Years)
Security Team Lead / Sr. Security Consultant (3-5 Years)
Security Consultant (1-3 Years)
Project Manager (2 - 4 Years)
Penetration Tester Consultant (2-4 years)
Lead Software Architect (10 years as a software developer, 3 years as a technical architect)
IT Analyst (1-2 Years)
Developer (3-5 Years)
Content Strategist & Editor (2-4 Years)
Role Summary:
As a wordpress developer, you would be responsible for the development, maintenance, and optimization of our company’s website. This role requires a strong understanding of web development technologies, content management systems, and a keen eye for design and user experience. You will play a crucial role in enhancing our online presence and ensuring a seamless user experience for our audience.
Mandatory Skill Sets/Expertise:
- Strong knowledge of web design principles and user experience best practices.
- Proficiency in web development languages (e.g., HTML, PHP, CSS, JavaScript)
- Proficiency in content management systems (e.g., WordPress, Drupal).
- Experience in managing Security tools – AV, MDM & DLP
Key Attributes:
- Proven experience in web development and content management.
- Familiarity with SEO strategies and tools.
- Excellent problem-solving skills and attention to detail.
- Strong communication and collaboration abilities.
- Ability to adapt to evolving web technologies and industry trends.
Key Responsibilities:
- Website development – Plan and execute website development projects. Develop and implement new website features, pages, and functionalities. Optimize user experience, including site navigation, page loading speed, and overall usability.
- In-depth expertise in WordPress – Demonstrate expertise in developing and customizing WordPress themes, plugins, and templates. The candidates should be proficient in PHP, HTML, CSS, and JavaScript, and have hands-on experience with popular WordPress frameworks and libraries.
- Multisite Management – Strong experience in efficiently managing WordPress multisite networks, including setup, configuration, maintenance, ensuring their stability and optimal performance. Implement A/B testing and gather user feedback to make data-driven improvements.
- Security and Maintenance – Ensure the security and integrity of WordPress installations by implementing best practices and staying updated with the latest security trends. Perform regular maintenance tasks to keep websites up-to-date and running smoothly.
- Server Management – Having hands-on experience in managing the Codes. Regularly update and maintain website content, including text, images, and multimedia elements
A day in the life
- Perform Penetration Testing for networks (internal & external), applications, APIs & cloud assets
along with Red & Purple Team assessments - Vulnerability identification and analysis
- Collaborate with team members and stakeholders to define project scopes, review test results,
and determine remediation steps - Draft reports and communicate complex security concepts and test findings to clients and
stakeholders - Make expert recommendations to help clients improve their information security program
- Work on researching & developing utilities, toolkits, processes, tactics, and techniques
Qualifications & Requirements
- 5-7 years of penetration testing experience, preferably in highly regulated industries and for
global clients - At least 2-3 years of experience in managing a team is a plus
- Proficiency with scripting and programming languages
- Advanced problem-solving skills
- OSCP/OSWE certification preferred but, GPEN, GWAPT, GXPN, CREST, CESG, and similar
certifications are a plus - Experience with Cobalt Strike a plus
- Strong written and verbal communication skills
- Ability to work autonomously with little directional oversight
- Ability to lead a project and multiple testers
- Commitment to quality and on-schedule delivery; and a proven ability to establish and meet
milestones and deadlines - Customer-focused mentality to understand and appropriately respond to customers’ business
needs
Role Summary
The senior manager is responsible for leading and sustaining the team that drives the compliance strategy by working collaboratively with internal teams, SMEs, external customers, vendors, auditors and other stakeholders. He/she should be able to work collaboratively with other departments and stakeholders to achieve company-wide goals and satisfy the client.
Mandatory Skill Sets/Expertise
- Relevant bachelor’s or master’s degree in computer science/ IT Auditing/ Information Systems/ Privacy.
- Have at least 5-7 years of relevant information security auditing experience and advanced knowledge of general controls (security, change management, disaster backup recovery, data centre, infrastructure, etc.), IT governance processes (ITIL).
- Ability to critically review security policies and procedures, design and implementation of security policies, procedures, standards and controls in line with regulation and/or current standards.
- Good understanding and implementation expertise of industry standards in cybersecurity (ISO, ITIL, NIST, ISF, SOC, HITRUST, PCI DSS, HIPAA) and privacy (GDPR, ISO 27018) is an advantage.
- Good project management skills with the ability to collaborate with teams across multiple locations and a strong command of the English language.
- Relevant industry recognized certifications such as CISSP/CISA/CISM.
Key Attributes
- Leadership: To lead by example, collaborate with the team, and make appropriate decisions when required. effectively communicate the vision and goals of the Accorian.
- Mentoring: To mentor individuals from graduate to industry qualified, with the aim of motivating and enhancing their personal and professional development.
- Communication: To communicate effectively both verbally and in writing, with the team and clients, sharing information in a clear and concise manner.
- Problem-solving: Strong analytical skills to identify and solve complex problems within the GRC domain.
Key Responsibilities
- Setting strategic direction for audit readiness, managing compliance programs, driving continuous improvement activities, & reporting metrics.
- Interfacing with stakeholders, articulating control implementation and impact, and establishing considerations for applying security and compliance concepts to a technical cloud environment.
- Effectively communicating compliance program results, including assessment status, workflow, remediation, and reporting, to a broad audience including peers, senior and executive leaders.
- Leading small teams by assigning and tracking individual tasks and ensuring the team meets milestones and addresses challenges.
- Coordinating the overarching annual audit plan with internal and external auditors to support delivery of multiple, simultaneous audits and certifications.
- Supporting delivery of audit milestones to ensure audit timelines stay on target by proactively identifying and coordination resolution of roadblocks.
- Collaborating cross-functionally with technology and business stakeholders to drive, track, and resolve all aspects of compliance readiness and audit execution
Role Summary:
The Sr. Security Consultant / Team Leader is responsible for leading a team of Security Consultants, managing team and professional development goals, ensuring on-time delivery of GRC projects, and providing expert guidance to team members on GRC-related matters.
Mandatory Skill Sets/Expertise
- Relevant bachelor’s or master’s degree in computer science/ IT Auditing/ Information Systems/ Privacy.
- Have a minimum of 3-5 years of experience in the domain of cybersecurity and privacy.
- Experience in information security standards and best practices (ISO 27001, SOC 2, NIST, HIPAA, PCI DSS, HITRUST, etc).
- Experience in performing assessments and audits.
- Deep understanding of risk management principles and IT controls.
- Certified in relevant and industry recognized certifications.
Key Attributes:
- Leadership: To lead by example, collaborate with the team, and make appropriate decisions when required. effectively communicate the vision and goals of the Accorian.
- Mentoring: To mentor individuals from graduate to industry qualified, with the aim of motivating and enhancing their personal and professional development.
- Communication: To communicate effectively both verbally and in writing, with the team and clients, sharing information in a clear and concise manner.
- Problem-solving: Strong analytical skills to identify and solve complex problems within the GRC domain.
Key Responsibilities:
- Assessing cybersecurity risks and vulnerabilities and partnering with the security team to identify and analyze potential threats, evaluating their impact and likelihood of occurrence.
- Developing and implementing GRC strategies to analyze industry regulations and standards relevant to cybersecurity, translating them into practical policies and procedures for our organization.
- End to End Implementation of various standards, regulatory and compliance requirements such as SOC 2, HIPAA, HITRUST, NIST CSF, ISO 27001.
- Conducting GRC audits and collaborating and performing regular evaluations of our security controls and compliance measures, identifying gaps, and recommending improvements.
- Collaborating with strategic-integration and fostering strong relationships across various departments (IT, security, legal, compliance) to ensure seamless integration of GRC processes and cybersecurity initiatives.
- Provide expert advice on GRC strategies, frameworks, and methodologies to clients.
- Collaborate with internal and external auditors, providing necessary documentation and support for audits.
- Ensure clients’ adherence to relevant regulations, standards, and industry-specific compliance requirements.
- Developing and delivering training programs to educate employees on cybersecurity best practices and compliance requirements, promoting a culture of security awareness.
- Staying informed on emerging threats and regulations and continuously update your knowledge on the evolving cybersecurity landscape and adapt your strategies accordingly.
- Coordinating the overarching annual audit plan with internal and external auditors to support delivery of multiple, simultaneous audits and certifications.
- Supporting delivery of audit milestones to ensure audit timelines stay on target by proactively identifying and coordination resolution of roadblocks
Role Summary
Accorian is actively seeking for a dynamic and seasoned Consultant/Senior Consultant specializing in
the Governance, Risk, and Compliance (GRC) domain to join our team. The preferred candidate will
assume a pivotal role in providing strategic guidance to clients regarding the implementation of sound
risk management practices overseeing vendor relationships, conducting audits across various
frameworks, and harnessing the capabilities of the GRC tool. This multifaceted position necessitates a
profound comprehension of GRC principles, regulatory compliance, and the ability to implement
resilient risk management strategies. Collaborate extensively with cross-functional teams, conduct
evaluations of organizational processes, and deliver strategic recommendations aimed at enhancing
GRC frameworks.
Mandatory Skill Sets/Expertise
1. Bachelor’s or master’s degree in computer science, Information Security, Risk Management,
Cyberlaw, or a related field.
2. Proficient in leading GRC frameworks and methodologies (SOC, ISO 27001, HIPPA, NIST, PCI DSS,
etc.).
3. Strong understanding of cybersecurity frameworks and principles (e.g., NIST Cybersecurity
Framework, ISO 27001, HIPAA).
4. Familiarity with audit processes, internal controls, and assurance methodologies.
5. Experience with GRC software solutions (e.g. SAP GRC, ACL, Archer, etc.).
6. Knowledge of risk assessment, control design, and reporting methodologies
7. Ability to work independently and as part of a team.
Preferred Certifications: CISSP, ISO 27001 Lead Auditor or Implementer.
Key Attributes:
a. 1 – 3 years of experience in consulting or industry roles related to GRC.
b. Proven track record of successful GRC program implementation and optimization.
c. Customer-centric mindset with a focus on understanding and addressing clients’ unique needs.
d. Ability to translate complex technical concepts into clear and actionable insights for clients.
e. Passion for staying up to date on the latest trends and developments in GRC.
f. Strong work ethic and a commitment to delivering high-quality results.
g. Add on Strong project management skills to successfully lead and execute projects.
Key Responsibilities:
1. Assessing cybersecurity risks and vulnerabilities and partnering with the security team to identify
and analyze potential threats, evaluating their impact and likelihood of occurrence.
2. Developing and implementing GRC strategies to analyze industry regulations and standards
relevant to cybersecurity, translating them into practical policies and procedures for our
organization.
3. Conducting GRC audits and collaborating and performing regular evaluations of our security
controls and compliance measures, identifying gaps, and recommending improvements.
4. Collaborating with strategic-integration and fostering strong relationships across various
departments (IT, security, legal, compliance) to ensure seamless integration of GRC processes and
cybersecurity initiatives.
5. Provide expert advice on GRC strategies, frameworks, and methodologies to clients.
6. Collaborate with internal and external auditors, providing necessary documentation and support
for audits.
7. Ensure clients’ adherence to relevant regulations, standards, and industry-specific compliance
requirements.
8. Developing and delivering training programs to educate employees on cybersecurity best
practices and compliance requirements, promoting a culture of security awareness.
9. Staying informed on emerging threats and regulations and continuously update your knowledge
on the evolving cybersecurity landscape and adapt your strategies accordingly
Role Summary
The role of the Project Manager would be to help plan and track cybersecurity & technology projects to meet KRAs, milestones & deadlines. This would also include coordinating. meetings with clients & internal teams and resource planning. The primary KRA would be to ensure projects are delivered on a timely manner and all stakeholders. are updated about the latest status of the project.
Mandatory Skill Sets/Expertise
- Great communication skills – written & oral
- At least 2 to 4 years of project coordination & management experience for technology consulting or implementation services.
- Strong planning, organizing, and execution skills
- Ability to work collaboratively with global teams & clients, and with staff of different backgrounds and experience levels along with managing goals.
- Strong interest in learning and developing professional skills
- Logical problem-solving skills; looks beyond immediate problems to consider root causes and addresses them.
- Possess a high degree of personal responsibility.
- Must have completed graduation.
Key Attributes
- Excellent communication skills
- Strategic thinking and visioning
- Excellent attention to detail
Key Responsibilities: –
- Provide support and assistance to the program and aid by tracking.
- Completion of all required tasks to meet project and client goals.
- Foresee; manage; and raise appropriate visibility to risks and issues.
- Drive resolution of any conflicts and escalate as needed to avoid roadblocks.
- Drive execution rigor using set practices; Manage & Drive Change wherever needed.
- Generate and publish weekly reports; corporate process improvements in developing new reports.
- Organizing, attending, and participating in stakeholder meetings.
- Documenting and following up on important actions and decisions from meetings.
- Developing project strategies
- Ensuring projects adhere to our clients’ frameworks and all documentation is maintained. appropriately for each project
- Ensure stakeholder views are managed towards the best solution.
- Chair and facilitate meetings where appropriate; distribute minutes to all project team.
- Track deliverables and calendar timelines
A day in the life
- Perform Penetration Testing for networks (internal & external), applications, APIs & cloud assets along with Red & Purple
Team assessments - Vulnerability identification and analysis
- Collaborate with team members and stakeholders to define project scopes, review test results,
and determine remediation steps - Draft reports and communicate complex security concepts and test findings to clients and
stakeholders - Make expert recommendations to help clients improve their information security program
- Work on researching & developing utilities, toolkits, processes, tactics, and techniques
Qualifications & Requirements
- 2-4 years of penetration testing experience, preferably in highly regulated industries and for global clients
- Proficiency with scripting and programming languages
- Advanced problem-solving skills
- OSCP certification preferred but, GPEN, GWAPT, GXPN, CREST, CESG and similar certifications a plus
- Experience with Cobalt Strike a plus
- Strong written and verbal communication skills
- Ability to work autonomously with little directional oversight
- Ability to lead a project and multiple testers
- Commitment to quality and on-schedule delivery; and a proven ability to establish and meet milestones and deadlines
- Customer-focused mentality to understand and appropriately respond to customers’ business needs
Role Summary:
As the Lead Software Architect, you will be a key leader in the development and evolution of our B2B SaaS product & it’s associated systems. The entire development team will report to you.
Drawing upon your extensive technical expertise and industry knowledge, you will design and implement scalable, robust, and efficient software solutions. Collaboration with cross-functional teams, technical leadership, and staying abreast of emerging technologies will be essential for success in this role.
About Our Product:
GORICO was incepted by security practitioners & audits with decades of experience to simplify the security conundrum and streamline the security compliance and security maintenance process. Security is a growth enabler today as it’s table stakes for doing business and a mandatory requirement as part of the third-party risk strategy of clients.
This is a single solution tailored to an organization to manage all your security adherence, compliance, vendor risk, vulnerability management , policy & procedure management and risk assessment needs.
It enables behaviour change and shift in the mindset towards security. It’s the only way to address the current reactive approach to it. Hence, going from a once a year or, couple of times a year audit rush to year long sustenance of security.
Hence, GORICO empowers organizations to understand, attain and sustain true security.
Mandatory Skill Sets/Expertise
- Proven experience as a Software Architect, with a track record of successful project delivery. A minimum of 2-3 years in this role
- Proven experience of building a B2B SaaS/Enterprise product
- Should’ve managed a software development team
- Strong proficiency in software design principles, patterns, and architectural best practices
- Expertise in multiple programming languages and frameworks including Node.js, React.js, Express, PostGreSQL
- Experience in integrating with APIs, SaaS solutions, ETL platforms
- Experience with AWS
- In-depth knowledge of database design, cloud computing, and microservices architecture
- Excellent problem-solving and analytical skills
Key Attributes
- Strategic thinking and vision
- Strong leadership and communication skills
- Adaptability and willingness to learn new technologies
- Detail-oriented and committed to delivering high-quality solutions
- Ability to collaborate effectively in a team environment
Key Responsibilities
- Architectural Design & SDLC:
- Review existing architecture and oversee areas of improvement
- Lead the design and development of new features and enhancements
- Define and document high-level architecture, including system components, modules, and interactions
- Lead the entire SDLC lifecycle and be hands on as the lead for the development team
- Technical Leadership:
- Provide technical leadership and guidance to the development teams
- Mentor and coach team members, fostering a culture of innovation and excellence
- System Integration:
- Collaborate with stakeholders, including the product manager, engineers, and internal teams, to ensure seamless integration of software components
- Design and implement interfaces and integration points between various system modules
- Scalability and Performance:
- Design scalable and high-performance software solutions that meet current and future business needs
- Conduct performance analysis and optimization to enhance system efficiency
- Technology Selection:
- Stay current with industry trends and emerging technologies
- Evaluate and recommend technologies, tools, and frameworks that align with business objectives
- Ability to substantiate and take build-vs-buy decisions
- Security and Compliance:
- Integrate security best practices into the software architecture
- Ensure compliance with relevant industry standards and regulations
- Code Review and Quality Assurance:
- Conduct code reviews to ensure adherence to architectural guidelines and best practices
- Assist QA team members to establish and maintain quality standards
- Documentation:
- Document architectural decisions, designs, and guidelines
- Prepare technical documentation for both internal and external audiences
- Feedback & Enhancement:
- Analyses market & user research to make data-driven decisions ▪ Implement feedback from clients
Role Summary:
As an IT Engineer, you will play a pivotal role in providing technical support to our internal members and ensuring the smooth operation of our IT environment. You will work under the guidance of IT Manager to resolve technical issues, help end-users, and contribute to the overall success of our IT support team
Mandatory Skill Sets/Expertise
- 1-2 years’ experience in IT Support or a related role
- Strong knowledge of Windows and/or Mac operating systems
- Proficiency in troubleshooting hardware and software issues
- Familiarity with network configurations and protocols
- Certifications such as CompTIA A+ or Microsoft Certified Desktop Support Technician (MCDST) is a plus
- Willingness to learn and adapt to new technologies and methodologies
- Strong problem-solving and analytical skills Key Attributes
- Good communication and customer service skills
- Adaptability and willingness to learn new technologies
- Detail-oriented and committed to delivering high-quality solutions
- Ability to collaborate effectively in a team environment
Key Responsibilities
- Provide first-level technical support to end-users, both remotely and on-site
- Assist with the installation, configuration, and maintenance of hardware and software
- Troubleshoot and resolve hardware/software issues in a timely manner
- Monitor and respond to IT service requests and incidents
- Maintain accurate and up-to-date records of Assets, support requests, incidents, and resolutions
- Assist with user account management and access control
- Ensure IT security and compliance measures are adhered to
- Participate in IT projects, such as system upgrades and deployments
- Assist in creating and updating IT documentation and knowledge base articles
- Stay up to date with the latest technology trends and best practice
Role Summary
As a developer, you will be responsible for designing, coding, testing, modifying and implementing new features in the B2B SaaS product. You would closely work with the technical architect towards building a scalable GRC tool.
Mandatory Skill Sets/Expertise
- Proven experience as a developer, with a track record of building scalable B2B SaaS/Enterprise product
- Strong coding skills in Node.js, React.js, Express, PostGreSQL
- Expertise in multiple programming languages and frameworks including
- Experience in integrating with APIs, SaaS solutions, ETL platforms
- Experience with AWS
- In-depth knowledge of database design, cloud computing, and microservices architecture
- Excellent problem-solving and analytical skills
Key Attributes
- Excellent coding skills
- Good communication skills
- Strong analytical and problem-solving skills
- Adaptability and willingness to learn new technologies
- Detail-oriented and committed to delivering high-quality solutions
- Ability to collaborate effectively in a team environment
Key Responsibilities
- Experience in developing B2B SaaS /Enterprise products using Node Js and React Js
- Manage code deployments, fixe, updates and other related processes
- Produce scalable code as per product and business requirement
- Troubleshooting, debugging, maintaining and improving the existing product
- Responsible for developing technical documentation to guide future product development
- Conduct performance analysis and optimization to enhance system efficiency
Role Summary
As a Content Strategist & Editor, you would be responsible for strategizing and creating high quality, engaging and informative content including blog spots, articles, product/service descriptions and other forms of digital and print media. You would be responsible for enhancing the brand awareness of Accorian whereby contributing towards lead generation from prospective customers.
Mandatory Skill Sets/Expertise
- Master of spelling, grammar, and punctuation
- Holds a keen interest in reading and has a high level of comprehension
- Thorough grasp of the English language with advanced vocabulary and grammar
- Ability to summarize information without losing the original meaning
- Understand trending technological and business concepts correctly, write compelling copy for popular concepts
- Proficiency with software/applications such as Microsoft Word, Excel, PowerPoint
- Experience working in a start-up environment
- Ability to actively participate in the adoption of digital tools and strategies
- Preferred experience – creation of knowledge library
- Ability to bring in language and content standardization in presentations, documentation, and reports.
- Ability to work on multiple projects with different objectives simultaneously Key Attributes
- Excellent communication skills (written as well as verbal)
- Excellent attention to detail
- Business acumen
Key Responsibilities
- Conduct extensive research and interviews to ensure content is accurate and up-to-date
- Engage readers with an informative, entertaining, and educational copy
- Understand and consistently reflect the branding of the company
- Work closely with internal stakeholders and external subject matter experts to develop content
- Proofread to standardize existing documents and edit at various stages of the writing process in response to feedback from internal management
- Conduct spot checks to evaluate quality of work
- Resolve queries, especially those related to language and style
- Should be able to give eye-catchy headlines and provide keywords on a regular basis
- Coordinating and contributing to proposal production while working collaboratively with other team members
- Work on presentations by evaluating texts and graphics
- Performing plagiarism checks
- Review of text/content going on various social media platforms of Accorian
Drop your CVs to joinourteam@accorian.com
Interested Position

