Article
NIST SP 800-39 - The Framework of Security
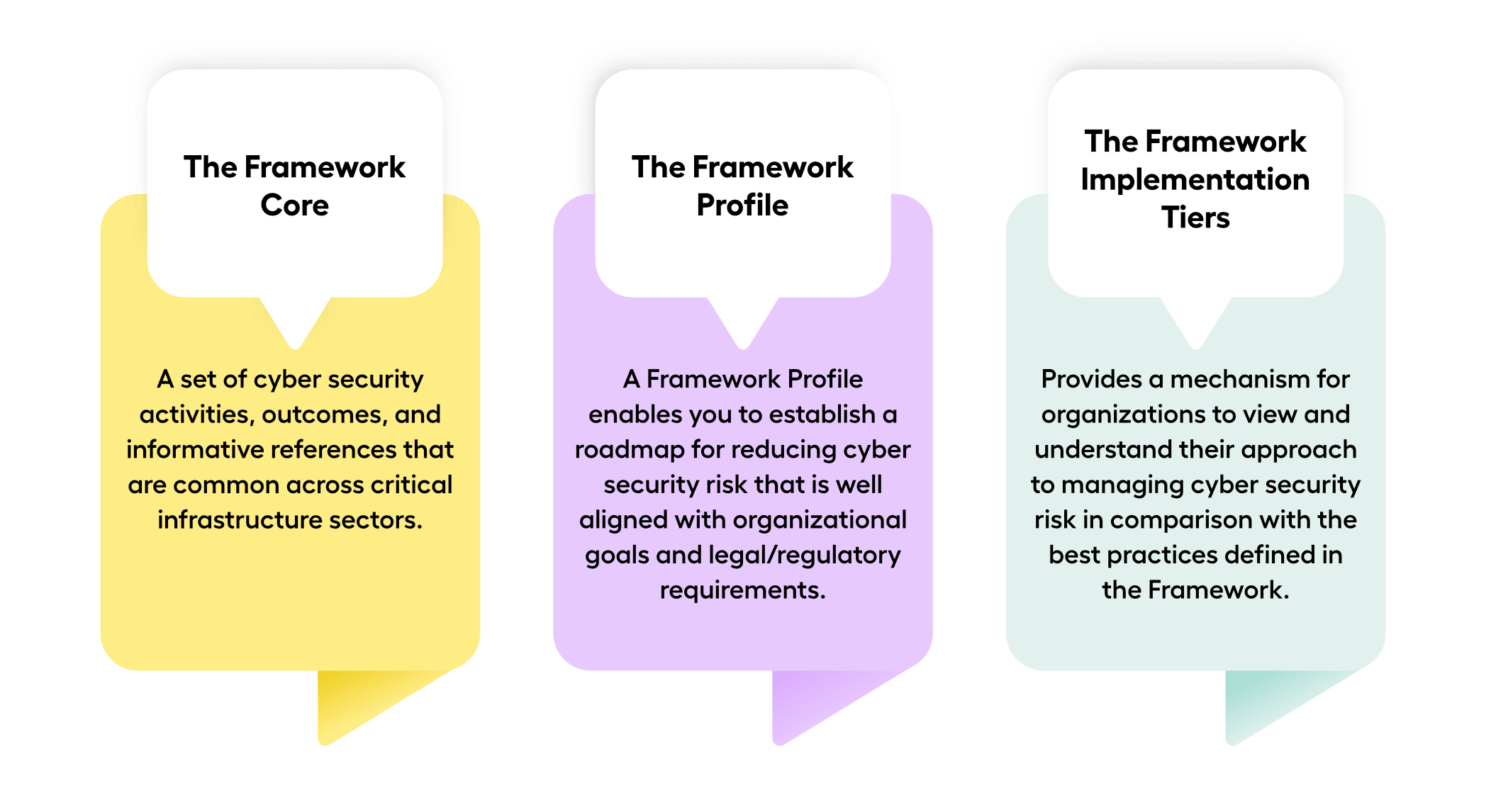
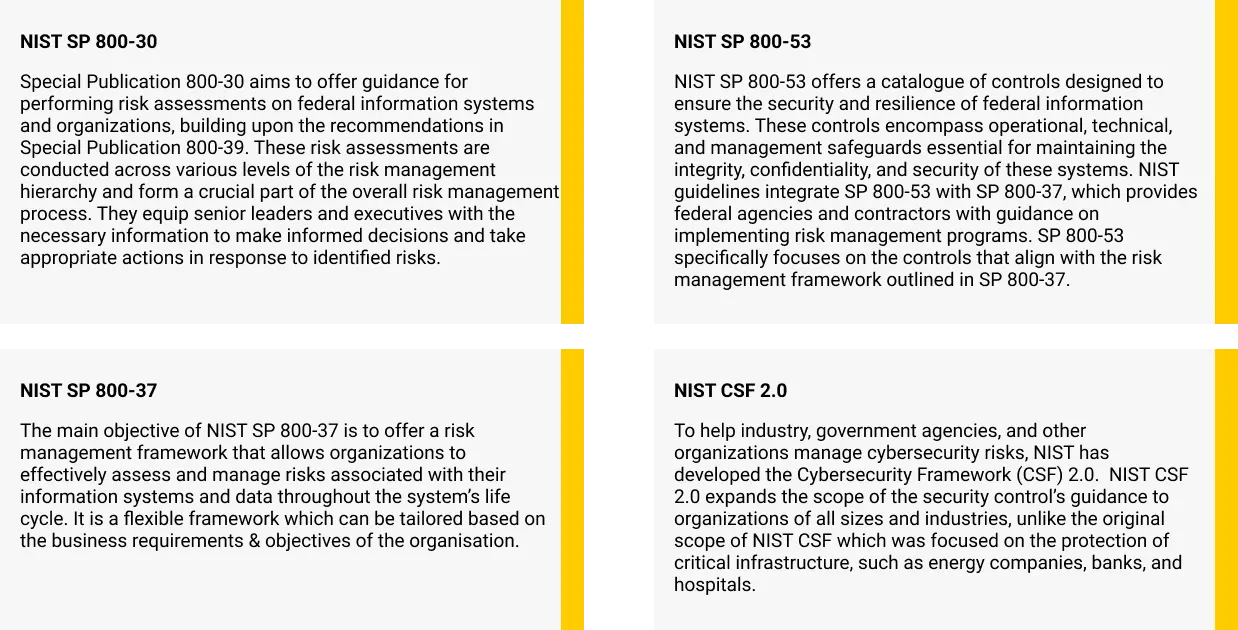
Written By: Vigneswar Ravi & Vedashree Venkatesh The ever-changing digital landscape poses a rising security challenge for organizations. Data security is not just a priority; it's a necessity. It must be effectively integrated with development objectives to ensure alignment and effectiveness. According to a recent IBM report, the average data breach cost in 2023 was $4.35 million, emphasizing the importance of robust information security measures. The National Institute of Standards and Technology (NIST) SP 800-39, released in 2011, is a valuable resource in the ongoing battle for data security. The National Institute of Standards and Technology Special Publication (NIST SP) 800-39 is an exhaustive guide for incorporating information security into organizational architecture. This document enables organizations of any size or industry to efficiently manage risks to assets, operations, and information systems. Why Do You Need Robust Information Security Practices? Robust information security practices are a strategic approach against the complexity and evolution of cybersecurity risks. As technology becomes more prevalent, the risk of cyberattacks rises dramatically. Enterprises can secure sensitive data, maintain regulatory compliance, ensure business continuity during disruptions, and create stakeholder trust by actively detecting vulnerabilities, assessing risks, and implementing focused mitigation techniques. Types of NIST 800-39 NIST Special Publication 800-39 is divided into volumes, each focusing on a different facet of data security. Despite this division, the publication provides comprehensive guidance for managing risks related to data security. These comprise: NIST 800-39 Volume 1</h2 > Handbook for Risk Assessments NIST 800-39 Volume 2</h2 > Handbook for Using the Risk Management Framework with Federal Information Systems NIST 800-39 Volume 3</h2 > Handbook for Evaluating Security Controls in Federal Information Systems and Organizations NIST 800-39 Volume 4</h2 > Handbook for Security Authorization of Federal Information Systems Understanding the Risk Management Framework (RMF) in NIST 800-39 NIST Special Publication 800-39 offers guidance on risk management for information systems. Organizations can enhance their risk management compliance and cybersecurity posture by understanding the essential elements of NIST 800-39. By categorizing systems, organizations can identify the right level of protection necessary. The RMF consists of several measures that assist organizations in consistently and fully implementing risk management practices. Benefits of Implementing NIST 800 – 39 Enhanced Risk Management Improved Security Posture Regulatory Compliance Proactive Threat Management Continuous Improvement Resilience Benefits Beyond Compliance While consistency is a significant driver for adopting the NIST Special Publication 800-39 framework, numerous additional benefits extend beyond consistency. Associations can: Reduce Security Risks: </h2 > Proactive risk management helps prevent security breaches and minimizes potential damage Improve Data Protection: </h2 > Enhanced security measures ensure better sensitive information and data protection Boost Operational Efficiency: </h2 > Optimized resource allocation and streamlined security processes lead to improved operational efficiency Build Trust and Confidence: </h2 > Strong information security practices foster trust with stakeholders, customers, and partners
View More