⚠️ Hiring Scam Alert: Accorian only recruits with our internal HR and Talent Acquisition team. We do not charge candidates at any point during recruitment. Check any communication that claims to be from Accorian and is suspicious. Accorian is not liable for fake offers or recruitment scams by third parties.
⚠️ Hiring Scam Alert: Accorian only recruits with our internal HR and Talent Acquisition team. We do not charge candidates at any point during recruitment. Check any communication that claims to be from Accorian and is suspicious. Accorian is not liable for fake offers or recruitment scams by third parties.
Human-Led Expertise.
AI-Powered Efficiency.
Product-Driven Trust.
One of 10 accredited organizations offering both audit and testing services on a unified platform.
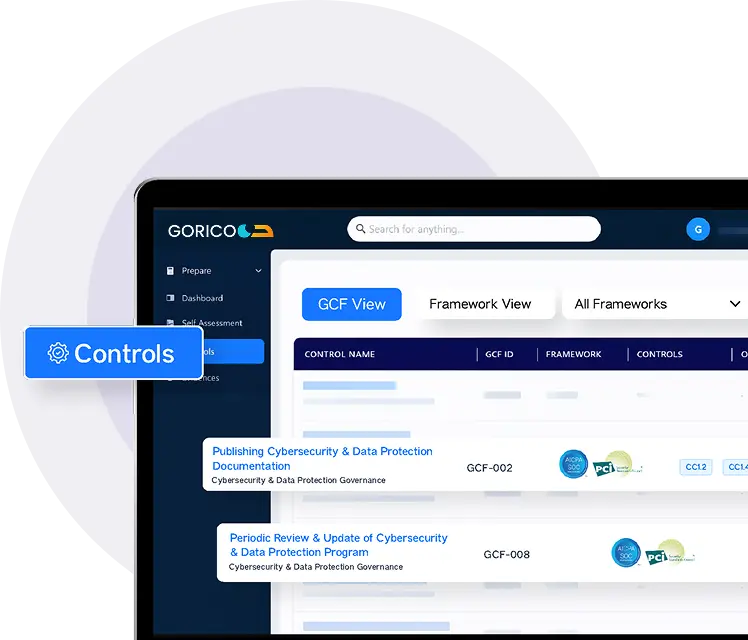
Accorian delivers comprehensive Security and Compliance Services, including Penetration Testing, Third-Party Risk Management (TPRM), Compliance services, AI risk management, and vCISO advisory. This is facilitated by our AI-enabled unified platform GORICO that helps reduce risk, accelerate certification, and build a resilient security posture.
TRUE SECURITY STARTS HERE




Where Expertise
Meets Automation
Accorian integrates deep cybersecurity and compliance expertise with our AI-enabled platform, GORICO, to move organizations beyond point-in-time audits toward continuous risk intelligence and real-time compliance visibility.
By embedding controls, centralizing evidence, and enabling ongoing monitoring, GORICO transforms compliance from a reactive exercise into a sustained governance advantage.
CONTINUOUS COMPLIANCE SIMPLIFIED
- Centralized Risk Registration
- Automated Evidence Collection
- Real-Time Compliance Posture
- Policy Lifecycle Management
- Third-Party Oversight
- AI-Governance Tracing
FRAMEWORKS
Evidence Reusability
INTEGRATIONS
Hours SAVED
Our Core Services
- Finance
- Health
- Manufacturing
- Media
- MSPs
- Retail & eCommerce
- SaaS And Technology
- SLED
- VC & Private Equity
- Accorian’s Multi-Compliance Framework
- AI Chatbot Penetration Testing
- Application Penetration Testing
- Cloud Security
- DevSecOps
- EU CRA (EU Cyber Resilience Act)
- External Network Penetration Testing
- GDPR
- Internal Network Penetration Testing
- ISO 22301
- ISO 27001
- ISO 27017
- ISO 27018
- ISO 27701
- ISO 31000
- ISO 42001
- Managed TPRM
- Multi-Compliance Bundle
- NIST AI 100-1
- NIST AI RMF
- NIST CSF
- NIST CSF 2.0
- NIST SP 800-30
- NIST SP 800-37
- NIST SP 800-53
- PCI ASV
- PCI DSS
- Penetration Testing
- Phishing / Vishing / Social Engineering
- Posture Assessment
- Product Suite Security
- Ransomware Assessment
- Red Teaming
- Risk Assessment
- Secure Code Review
- Security Strategy
- SOC 1
- SOC 2
- vCISO & vSecurity Team
- Wireless Network Penetration Testing
- Accorian’s Multi-Compliance Framework
- AI Chatbot Penetration Testing
- Application Penetration Testing
- Cloud Security
- DevSecOps
- EU CRA (EU Cyber Resilience Act)
- External Network Penetration Testing
- GDPR
- HIPAA
- HITRUST
- Internal Network Penetration Testing
- ISO 22301
- ISO 27001
- ISO 27017
- ISO 27018
- ISO 27701
- ISO 31000
- ISO 42001
- Managed TPRM
- Multi-Compliance Bundle
- NIST AI 100-1
- NIST AI RMF
- NIST CSF
- NIST CSF 2.0
- NIST SP 800-30
- NIST SP 800-37
- NIST SP 800-53
- PCI ASV
- PCI DSS
- Penetration Testing
- Phishing / Vishing / Social Engineering
- Posture Assessment
- Product Suite Security
- Ransomware Assessment
- Red Teaming
- Risk Assessment
- Secure Code Review
- Security Strategy
- SOC 2
- vCISO & vSecurity Team
- Wireless Network Penetration Testing
- Accorian’s Multi-Compliance Framework
- Application Penetration Testing
- Cloud Security
- DevSecOps
- EU CRA (EU Cyber Resilience Act)
- External Network Penetration Testing
- GDPR
- Internal Network Penetration Testing
- ISO 22301
- ISO 27001
- ISO 27017
- ISO 31000
- Managed TPRM
- Multi-Compliance Bundle
- NIST AI 100-1
- NIST AI RMF
- NIST CSF
- NIST CSF 2.0
- NIST SP 800-171
- NIST SP 800-30
- NIST SP 800-37
- PCI ASV
- PCI DSS
- Penetration Testing
- Phishing / Vishing / Social Engineering
- Product Suite Security
- Ransomware Assessment
- Red Teaming
- Risk Assessment
- Secure Code Review
- Security Strategy
- vCISO & vSecurity Team
- Wireless Network Penetration Testing
- Accorian’s Multi-Compliance Framework
- AI Chatbot Penetration Testing
- Application Penetration Testing
- Cloud Security
- DevSecOps
- EU CRA (EU Cyber Resilience Act)
- External Network Penetration Testing
- GDPR
- Internal Network Penetration Testing
- ISO 22301
- ISO 27001
- ISO 27017
- ISO 27018
- ISO 27701
- ISO 42001
- Managed TPRM
- Multi-Compliance Bundle
- NIST CSF
- NIST CSF 2.0
- NIST SP 800-30
- PCI ASV
- PCI DSS
- Penetration Testing
- Phishing / Vishing / Social Engineering
- Posture Assessment
- Product Suite Security
- Ransomware Assessment
- Risk Assessment
- Secure Code Review
- Security Strategy
- SOC 2
- vCISO & vSecurity Team
- Wireless Network Penetration Testing
- Accorian’s Multi-Compliance Framework
- AI Chatbot Penetration Testing
- Application Penetration Testing
- Cloud Security
- CMMC
- DevSecOps
- EU CRA (EU Cyber Resilience Act)
- External Network Penetration Testing
- GDPR
- HIPAA
- HITRUST
- Internal Network Penetration Testing
- ISO 22301
- ISO 27001
- ISO 27017
- ISO 27018
- ISO 27701
- ISO 31000
- ISO 42001
- Managed TPRM
- Multi-Compliance Bundle
- NIST AI 100-1
- NIST AI RMF
- NIST CSF
- NIST CSF 2.0
- NIST SP 800-171
- NIST SP 800-30
- PCI ASV
- PCI DSS
- Penetration Testing
- Phishing / Vishing / Social Engineering
- Posture Assessment
- Product Suite Security
- Ransomware Assessment
- Risk Assessment
- Secure Code Review
- Security Strategy
- SOC 1
- SOC 2
- vCISO & vSecurity Team
- Wireless Network Penetration Testing
- Accorian’s Multi-Compliance Framework
- AI Chatbot Penetration Testing
- Application Penetration Testing
- Cloud Security
- DevSecOps
- EU CRA (EU Cyber Resilience Act)
- External Network Penetration Testing
- GDPR
- Internal Network Penetration Testing
- ISO 22301
- ISO 27001
- ISO 27017
- ISO 27018
- ISO 27701
- ISO 31000
- ISO 42001
- Managed TPRM
- Multi-Compliance Bundle
- NIST AI 100-1
- NIST AI RMF
- NIST CSF
- NIST CSF 2.0
- NIST SP 800-30
- PCI ASV
- PCI DSS
- Phishing / Vishing / Social Engineering
- Posture Assessment
- Product Suite Security
- Ransomware Assessment
- Red Teaming
- Risk Assessment
- Secure Code Review
- Security Strategy
- SOC 1
- SOC 2
- vCISO & vSecurity Team
- Wireless Network Penetration Testing
- Accorian’s Multi-Compliance Framework
- AI Chatbot Penetration Testing
- Application Penetration Testing
- Cloud Security
- CMMC
- DevSecOps
- EU CRA (EU Cyber Resilience Act)
- External Network Penetration Testing
- GDPR
- HITRUST
- Internal Network Penetration Testing
- ISO 22301
- ISO 27001
- ISO 27017
- ISO 27018
- ISO 27701
- ISO 31000
- ISO 42001
- Managed TPRM
- Multi-Compliance Bundle
- NIST AI 100-1
- NIST AI RMF
- NIST CSF
- NIST CSF 2.0
- NIST SP 800-30
- NIST SP 800-37
- NIST SP 800-53
- PCI ASV
- PCI DSS
- Penetration Testing
- Phishing / Vishing / Social Engineering
- Posture Assessment
- Product Suite Security
- Ransomware Assessment
- Red Teaming
- Risk Assessment
- Secure Code Review
- Security Strategy
- SOC 1
- SOC 2
- vCISO & vSecurity Team
- Wireless Network Penetration Testing
- Accorian’s Multi-Compliance Framework
- Application Penetration Testing
- Cloud Security
- DevSecOps
- EU CRA (EU Cyber Resilience Act)
- External Network Penetration Testing
- Internal Network Penetration Testing
- ISO 22301
- ISO 27001
- ISO 27017
- ISO 27018
- ISO 27701
- ISO 31000
- ISO 42001
- Managed TPRM
- Multi-Compliance Bundle
- NIST AI 100-1
- NIST AI RMF
- NIST CSF
- NIST CSF 2.0
- NIST SP 800-171
- NIST SP 800-30
- NIST SP 800-37
- NIST SP 800-53
- PCI ASV
- PCI DSS
- Penetration Testing
- Phishing / Vishing / Social Engineering
- Posture Assessment
- Product Suite Security
- Ransomware Assessment
- Red Teaming
- Risk Assessment
- Secure Code Review
- vCISO & vSecurity Team
- Wireless Network Penetration Testing
- Accorian’s Multi-Compliance Framework
- Application Penetration Testing
- Cloud Security
- CMMC
- EU CRA (EU Cyber Resilience Act)
- External Network Penetration Testing
- Internal Network Penetration Testing
- ISO 22301
- ISO 27001
- ISO 27017
- ISO 27018
- ISO 27701
- ISO 31000
- ISO 42001
- Managed TPRM
- Multi-Compliance Bundle
- NIST AI 100-1
- NIST AI RMF
- NIST CSF
- NIST CSF 2.0
- NIST SP 800-30
- NIST SP 800-37
- NIST SP 800-53
- PCI ASV
- PCI DSS
- Penetration Testing
- Phishing / Vishing / Social Engineering
- Posture Assessment
- Product Suite Security
- Ransomware Assessment
- Red Teaming
- Risk Assessment
- SOC 1
- SOC 2
- vCISO & vSecurity Team
- Accorian’s Multi-Compliance Framework
- AI Chatbot Penetration Testing
- Application Penetration Testing
- Cloud Security
- DevSecOps
- EU CRA (EU Cyber Resilience Act)
- External Network Penetration Testing
- GDPR
- Internal Network Penetration Testing
- ISO 22301
- ISO 27001
- ISO 27017
- ISO 27018
- ISO 27701
- ISO 31000
- ISO 42001
- Managed TPRM
- Multi-Compliance Bundle
- NIST AI 100-1
- NIST AI RMF
- NIST CSF
- NIST CSF 2.0
- NIST SP 800-30
- NIST SP 800-37
- NIST SP 800-53
- PCI ASV
- PCI DSS
- Penetration Testing
- Phishing / Vishing / Social Engineering
- Posture Assessment
- Product Suite Security
- Ransomware Assessment
- Red Teaming
- Risk Assessment
- Secure Code Review
- Security Strategy
- SOC 1
- SOC 2
- vCISO & vSecurity Team
- Wireless Network Penetration Testing
- Accorian’s Multi-Compliance Framework
- AI Chatbot Penetration Testing
- Application Penetration Testing
- Cloud Security
- DevSecOps
- EU CRA (EU Cyber Resilience Act)
- External Network Penetration Testing
- GDPR
- HIPAA
- HITRUST
- Internal Network Penetration Testing
- ISO 22301
- ISO 27001
- ISO 27017
- ISO 27018
- ISO 27701
- ISO 31000
- ISO 42001
- Managed TPRM
- Multi-Compliance Bundle
- NIST AI 100-1
- NIST AI RMF
- NIST CSF
- NIST CSF 2.0
- NIST SP 800-30
- NIST SP 800-37
- NIST SP 800-53
- PCI ASV
- PCI DSS
- Penetration Testing
- Phishing / Vishing / Social Engineering
- Posture Assessment
- Product Suite Security
- Ransomware Assessment
- Red Teaming
- Risk Assessment
- Secure Code Review
- Security Strategy
- SOC 2
- vCISO & vSecurity Team
- Wireless Network Penetration Testing
- Accorian’s Multi-Compliance Framework
- Application Penetration Testing
- Cloud Security
- DevSecOps
- EU CRA (EU Cyber Resilience Act)
- External Network Penetration Testing
- GDPR
- Internal Network Penetration Testing
- ISO 22301
- ISO 27001
- ISO 27017
- ISO 31000
- Managed TPRM
- Multi-Compliance Bundle
- NIST AI 100-1
- NIST AI RMF
- NIST CSF
- NIST CSF 2.0
- NIST SP 800-171
- NIST SP 800-30
- NIST SP 800-37
- PCI ASV
- PCI DSS
- Penetration Testing
- Phishing / Vishing / Social Engineering
- Product Suite Security
- Ransomware Assessment
- Red Teaming
- Risk Assessment
- Secure Code Review
- Security Strategy
- vCISO & vSecurity Team
- Wireless Network Penetration Testing
- Accorian’s Multi-Compliance Framework
- AI Chatbot Penetration Testing
- Application Penetration Testing
- Cloud Security
- DevSecOps
- EU CRA (EU Cyber Resilience Act)
- External Network Penetration Testing
- GDPR
- Internal Network Penetration Testing
- ISO 22301
- ISO 27001
- ISO 27017
- ISO 27018
- ISO 27701
- ISO 42001
- Managed TPRM
- Multi-Compliance Bundle
- NIST CSF
- NIST CSF 2.0
- NIST SP 800-30
- PCI ASV
- PCI DSS
- Penetration Testing
- Phishing / Vishing / Social Engineering
- Posture Assessment
- Product Suite Security
- Ransomware Assessment
- Risk Assessment
- Secure Code Review
- Security Strategy
- SOC 2
- vCISO & vSecurity Team
- Wireless Network Penetration Testing
- Accorian’s Multi-Compliance Framework
- AI Chatbot Penetration Testing
- Application Penetration Testing
- Cloud Security
- CMMC
- DevSecOps
- EU CRA (EU Cyber Resilience Act)
- External Network Penetration Testing
- GDPR
- HIPAA
- HITRUST
- Internal Network Penetration Testing
- ISO 22301
- ISO 27001
- ISO 27017
- ISO 27018
- ISO 27701
- ISO 31000
- ISO 42001
- Managed TPRM
- Multi-Compliance Bundle
- NIST AI 100-1
- NIST AI RMF
- NIST CSF
- NIST CSF 2.0
- NIST SP 800-171
- NIST SP 800-30
- PCI ASV
- PCI DSS
- Penetration Testing
- Phishing / Vishing / Social Engineering
- Posture Assessment
- Product Suite Security
- Ransomware Assessment
- Risk Assessment
- Secure Code Review
- Security Strategy
- SOC 1
- SOC 2
- vCISO & vSecurity Team
- Wireless Network Penetration Testing
- Accorian’s Multi-Compliance Framework
- AI Chatbot Penetration Testing
- Application Penetration Testing
- Cloud Security
- DevSecOps
- EU CRA (EU Cyber Resilience Act)
- External Network Penetration Testing
- GDPR
- Internal Network Penetration Testing
- ISO 22301
- ISO 27001
- ISO 27017
- ISO 27018
- ISO 27701
- ISO 31000
- ISO 42001
- Managed TPRM
- Multi-Compliance Bundle
- NIST AI 100-1
- NIST AI RMF
- NIST CSF
- NIST CSF 2.0
- NIST SP 800-30
- PCI ASV
- PCI DSS
- Phishing / Vishing / Social Engineering
- Posture Assessment
- Product Suite Security
- Ransomware Assessment
- Red Teaming
- Risk Assessment
- Secure Code Review
- Security Strategy
- SOC 1
- SOC 2
- vCISO & vSecurity Team
- Wireless Network Penetration Testing
- Accorian’s Multi-Compliance Framework
- AI Chatbot Penetration Testing
- Application Penetration Testing
- Cloud Security
- CMMC
- DevSecOps
- EU CRA (EU Cyber Resilience Act)
- External Network Penetration Testing
- GDPR
- HITRUST
- Internal Network Penetration Testing
- ISO 22301
- ISO 27001
- ISO 27017
- ISO 27018
- ISO 27701
- ISO 31000
- ISO 42001
- Managed TPRM
- Multi-Compliance Bundle
- NIST AI 100-1
- NIST AI RMF
- NIST CSF
- NIST CSF 2.0
- NIST SP 800-30
- NIST SP 800-37
- NIST SP 800-53
- PCI ASV
- PCI DSS
- Penetration Testing
- Phishing / Vishing / Social Engineering
- Posture Assessment
- Product Suite Security
- Ransomware Assessment
- Red Teaming
- Risk Assessment
- Secure Code Review
- Security Strategy
- SOC 1
- SOC 2
- vCISO & vSecurity Team
- Wireless Network Penetration Testing
- Accorian’s Multi-Compliance Framework
- Application Penetration Testing
- Cloud Security
- DevSecOps
- EU CRA (EU Cyber Resilience Act)
- External Network Penetration Testing
- Internal Network Penetration Testing
- ISO 22301
- ISO 27001
- ISO 27017
- ISO 27018
- ISO 27701
- ISO 31000
- ISO 42001
- Managed TPRM
- Multi-Compliance Bundle
- NIST AI 100-1
- NIST AI RMF
- NIST CSF
- NIST CSF 2.0
- NIST SP 800-171
- NIST SP 800-30
- NIST SP 800-37
- NIST SP 800-53
- PCI ASV
- PCI DSS
- Penetration Testing
- Phishing / Vishing / Social Engineering
- Posture Assessment
- Product Suite Security
- Ransomware Assessment
- Red Teaming
- Risk Assessment
- Secure Code Review
- vCISO & vSecurity Team
- Wireless Network Penetration Testing
- Accorian’s Multi-Compliance Framework
- Application Penetration Testing
- Cloud Security
- CMMC
- EU CRA (EU Cyber Resilience Act)
- External Network Penetration Testing
- Internal Network Penetration Testing
- ISO 22301
- ISO 27001
- ISO 27017
- ISO 27018
- ISO 27701
- ISO 31000
- ISO 42001
- Managed TPRM
- Multi-Compliance Bundle
- NIST AI 100-1
- NIST AI RMF
- NIST CSF
- NIST CSF 2.0
- NIST SP 800-30
- NIST SP 800-37
- NIST SP 800-53
- PCI ASV
- PCI DSS
- Penetration Testing
- Phishing / Vishing / Social Engineering
- Posture Assessment
- Product Suite Security
- Ransomware Assessment
- Red Teaming
- Risk Assessment
- SOC 1
- SOC 2
- vCISO & vSecurity Team
Trusted By Leading Clients

Accorian provided valuable support throughout our HITRUST e1 assessment. Their structured approach and clear guidance helped streamline the process and improve our overall readiness. The team was responsive and organized, enabling us to complete the assessment efficiently while minimizing disruption to our ongoing operations.
Harry Vijayakumar - Chief Information Officer
Lutheran Social Services of Illinois

The Accorian team quickly understood the complex risks around data exposure, privilege escalation, and multi-tenancy in our AI-driven product. Their approach wasn’t generic, they asked the right questions and delivered AI chatbot penetration testing that pushed our guardrails to the limit. Thanks to their work, we’ve significantly strengthened our security posture and feel more confident scaling in a rapidly evolving threat environment.
Andy Sen - Co-Founder / CTO
Precanto

Accorian's expert team had seamlessly integrated as our dedicated security experts, serving as both our SOC 2 auditors and virtual CISO. The implementation of GORICO and its thorough risk assessments has significantly strengthened our security operations. What sets them apart is their genuine investment in our success, they’ve proven to be true strategic partners in our security mission.
Trudy Janse van Rensburg
WNDYR

I sincerely appreciate Accorian’s partnership with WellStack in guiding us through the HITRUST, SOC 2 Type II, and HIPAA risk assessment journey. The process was smooth thanks to your timely guidance and dedication. Your team went above and beyond to ensure we had the right evidence in place and clearly explained each control, timeline, and scoring model. Thank you for being a true partner throughout the process.
Rakesh Rajasekharan - Sr. VP - Global Delivery
WellStack

Our firm has been working with the Accorian team for several years and we are highly satisfied with the work and our relationship with them. Their services are first rate and of the highest quality always providing high value. We recommend them highly.
Greg Ware - President & Founder
Net Compliance Solutions

TMRW worked with Accorian, a consultancy specializing in technology risk assessment and ISO 27001 readiness, to prepare for the audit. There was a rigorous process implemented to ensure maximum security across all aspects of the TMRW platform.
Amit Gupta - CIO
TMRW

I am pleased to say that we had a strong security framework in place at the beginning of our ISO journey and thanks to the diligent work of the team and guidance of Accorian, we proved we have a comprehensive IMMS in place that addresses our clients’ needs for confidentiality, integrity, and availability.
Brendon Sheideler - CIO
BlueMatrix

IMM started working with Accorian team few years ago to perform a Pen testing for our application and cloud infrastructure. Accorian team has done a great job in working with our engineering team to safeguard IMM’s application. Our collaborative work has yielded in additional product pen tests and now part of our DeVops process. Great Job Accorian team and happy to have you as our trusted 3rd party security team.
Nish Shah - CTO
IMM

We engaged with Accorian to streamline our security environment and safeguard us from long-term threats in an evolving cybersecurity landscape. Their sole focus was to ensure the breadth and depth of our systems were protected.
Jatin Mehta - Head of Engineering
Openroad Media

I have handled a few pen test engagements over the last few years and this was the best overall experience. Ashritha and her team genuinely care about the security of their clients, and ensure no stone is left unturned.
Zalman M - Security Manager
FinTech Co.

Our experience of working with Accorian was extremely positive. They quickly grasped the scale of our systems, project managed with clear deliverables, over communicated and ensured all our deadlines were met. The professionalism of the service provided was wonderful. I highly recommend Accorian to anyone in the future for business critical security needs.
Rajib Ahmed - CTO
Meetup

The SOC 2 Bundle has been an absolute game-changer for us! Accorian's seamless integration of automation and services streamlined our processes, eliminating the need for multiple vendors. This efficiently allowed us to focus on our objectives and fast-track our SOC journey without compromise.
John Lightfoot - CTO
Patient Engagement Advisors

We executed our annual penetration test with the help of Accorian's team. They were great to work with and provided a clear and detailed report that helped us strengthen the security profile of our apps and brand site. Their findings were current and included extremely clear explanations of the risks and the steps needed to remediate them. I rest easier knowing we've closed those issues.
Paul Degnan - Head of Engineering
OSHI Health

We love GORICO! It has streamlined our audit process with its intuitive interface and powerful features, making compliance management more efficient and less time-consuming. GORICO has transformed our approach to GRC, providing clarity and confidence in our compliance efforts.
Morgan Kershner - Security Officer
Novus Health Systems

Launching a healthcare business is challenging enough without managing PHI securely and compliantly. Finding a trusted partner was difficult until we were introduced to Accorian. As our HITRUST shepherds and assessors, their technical expertise, project management, and flexibility made them exceptional partners, guiding us patiently and expertly through the entire process.
Steven Waye - President & Chief Product Officer
AGATHOS
Get Started With Accorian
Where Expertise Meets Automation
GORICO - AI-enabled Platform
GORICO accelerates security and compliance execution by automating evidence orchestration, normalizing control data, and embedding intelligence directly into remediation workflows.
Exceptional Team
We are a team of 100+ security experts assisting multiple clients in meeting their security and certification requirements.
Comprehensive Services
As one of the 10 companies globally offering 12+ services, all under one roof, we provide a full range of security services to our clients, from security compliance, and consulting to pen testing and staffing.
Proven Process
Frequently Asked Questions (FAQs)
Q. How to get compliant?
A. Accorian guides you through the entire compliance journey, scoping, gap assessment, control implementation, audit preparation, and continuous monitoring. Our experts work alongside your team while GORICO tracks progress, evidence, and requirements in one centralized platform.
Q. What frameworks does Accorian support?
A. Accorian supports leading frameworks such as SOC 2, HITRUST, ISO 27001, HIPAA, PCI DSS, GDPR, and more. Our unified control mapping approach allows you to work toward multiple frameworks without duplicating effort.
Q. How long does it typically take to achieve compliance?
A. Timelines depend on your organization’s current maturity level, scope, and framework requirements. With structured workflows and guided implementation, Accorian helps streamline readiness and reduce delays commonly caused by manual processes.
Q. Is GORICO a GRC tool that supports compliance?
A. GORICO, Accorian’s AI-enabled GRC platform, centralizes risk management, compliance workflows, and audit readiness activities within a single environment. It enhances visibility into governance posture, automates evidence collection, and supports scalable multi-framework compliance, helping organizations reduce manual effort while improving control reliability.
Q. Can we do multiple certifications at the same time?
A. Yes, Accorian maps controls across frameworks so organizations can pursue multiple certifications efficiently. This reduces duplication of work and helps maintain consistency across regulatory requirements.
Q. How does Accorian help with audit preparation?
A. Accorian helps organize documentation, validate controls, and ensure evidence is audit-ready. GORICO tracks requirements and highlights gaps so teams can address issues before the audit begins.
Q. How do you manage vendor and third-party risk?
A. Vendors, suppliers, and technology partners often introduce unseen compliance exposure across security, privacy, and regulatory requirements. Accorian helps organizations proactively assess and continuously monitor third-party risk through structured frameworks and centralized visibility, ensuring external dependencies do not compromise internal compliance posture.
Q. Why do most compliance programs slow down innovation?
A. Compliance is often perceived as a bottleneck due to fragmented workflows, manual evidence collection, and a lack of centralized visibility into controls. Accorian transforms compliance into a strategic enabler by combining expert-led advisory with AI-enabled automation through GORICO. This unified approach reduces operational friction, improves efficiency, and enables organizations to scale securely without compromising speed.