Posture Assessment

In the ever-evolving cybersecurity landscape, where threats constantly mutate and evolve, businesses must adopt a strategic and calculated approach to safeguard their digital assets. A staggering 236.1 million ransomware attacks occurred globally in the first half of 2022, underscoring the pressing need for Posture Assessment.
Posture Assessment is a comprehensive evaluation of an organization’s cybersecurity readiness encompassing a multifaceted analysis of its technological landscape. This assessment systematically reviews the organization’s security controls, policies, processes, and infrastructure, aligning its technology landscape with the overall strategic objectives.
Why Posture Assessment?
Holistic Vulnerability Insight
A posture assessment is a strategic viewpoint that enables an organization to comprehend its susceptibility to cyber threats and vulnerabilities. Through a comprehensive examination of network configurations, system architectures, and application landscapes, businesses can obtain a holistic approach to potential weak points that malicious actors could exploit.
Strategic Risk Mitigation
Taking a proactive stance is paramount within the dynamic landscape of digital threats and countermeasures. Posture assessment empowers organizations with the tools to implement strategic risk mitigation strategies. It offers the intelligence required to prioritize and proactively address vulnerabilities before exploiting them, thus strengthening the organization’s digital perimeter.
Tailored Security Enhancement
Every organization possesses distinct security requirements, vulnerabilities, and strategic priorities. A posture assessment customizes security enhancements to align with an organization’s unique technological ecosystem. This tailored approach ensures that security measures are finely tuned to harmonize with the organization’s threat landscape.
Elevated Incident Response Preparedness
Just like the military trains units rigorously for emergencies, posture assessment drills an organization to respond effectively during an incident. These drills involve simulating potential attack scenarios and meticulously evaluating the effectiveness of response protocols. Through these exercises, organizations can hone their capability to promptly and adeptly counter cyber threats, ultimately enhancing their resilience in the face of unexpected challenges.
Regulatory Adherence and Compliance
In the cybersecurity landscape, regulatory compliance plays a crucial role. Posture assessment ensures that an organization adheres to applicable regulations and standards, reducing the risk of legal ramifications and monetary penalties.
Comprehensive Third-Party Risk Mitigation
Engaging in third-party services and collaborations introduces a unique set of potential risks that could damage the organization. Posture assessment extends its scope beyond internal operations, assessing the security postures of third-party vendors and partners. This vigilant scrutiny plays a crucial role in risk mitigation associated with external connections, safeguarding the organization’s interests and preserving the integrity of its collaborations and partnerships.
Posture Assessment Services
Following an organizational security posture assessment, Accorian provides diverse services to enhance cybersecurity further and fortify your organization’s defenses:
- Vulnerability Scanning
- Penetration Testing
- Risk Assessment (Asset and Smb based)
- Third Party Vendor Management
- Drafting Policies and Procedures
- End-to-End Cybersecurity Framework Audits/Certification
Accorian’s Posture Assessment Approach

- Questionnaire-based assessment
- The Posture Assessment Questionnaire incorporates insights gained from our extensive third-party assessment expertise. It draws upon various framework references, including NIST CSF, ISO 27001, SIG Lite, and other industry standards

- Interview of key stakeholders
- Review of responses
-
Audit of evidence to assess the effectiveness of implementation
& controls

- Delivering a comprehensive security posture report that includes overall score, domain-wise ratings, and actionable recommendations for addressing identified gaps
Accorian Assesses Your Organization’s
Security Posture Against 16 Domains
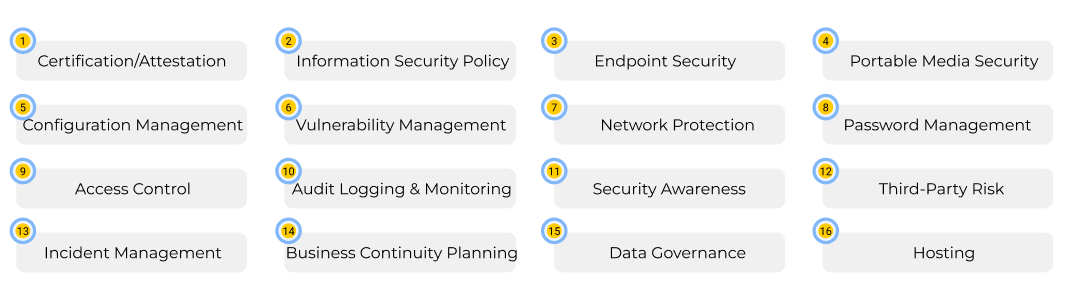
- Certification/Attestation
- Information Security Policy
- Endpoint Security
- Portable Media Security
- Configuration Management
- Vulnerability Management
- Network Protection
- Password Management
- Access Control
- Audit Logging & Monitoring
- Security Awareness
- Third-Party Risk
- Incident Management
- Business Continuity Planning
- Data Governance
- Hosting
Elevating Your Security Posture:
The Strategic Imperative
Incorporating security posture assessment into your organization’s strategic framework fortifies its cyber defense capabilities and fosters a culture of vigilance. This proactive approach safeguards your valuable assets, preserves your reputation, and bolsters the foundation for future growth and success. A security posture assessment can help you with the following:
1. Risk Identification
Identify potential security risks, threats, and vulnerabilities that are not readily apparent through routine security measures.
2. Prioritization
Allocate resources effectively by focusing on critical vulnerabilities and high-priority areas that demand immediate attention.
3. Proactive Approach
Detect and address security issues proactively, mitigating potential breaches and minimizing potential damage.
4. Incident Preparedness
Enhance your incident response plans by identifying gaps and refining strategies, ensuring adequate security breach mitigation.
5. Vendor Management
Evaluate the security of third-party vendors and partners, safeguarding your organization’s data across the entire supply chain.
6. Employee Awareness
Educate your employees about security best practices, empowering them to make informed decisions and reduce human-related security risks.
7. Continuous Improvement and Monitoring
Establish a cycle of improvement by regularly assessing and adapting security measures to evolving threats. Implement ongoing security monitoring and assessment to maintain a resilient posture.
8. Executive Decision-Making
Provide leadership with clear insights to make informed decisions regarding security investments and strategies.
9. Customer Trust
Demonstrate a commitment to data protection, fostering trust among customers, clients, and stakeholders.
10. Cost Efficiency
Avoid potential financial losses resulting from security breaches, which can outweigh the investment in assessment and mitigation.
11. Security Culture
Cultivate a security-conscious culture among employees, making security awareness an integral part of the organization’s identity.
12. Scalable Growth
Build a strong foundation for secure expansion, ensuring security measures align with your growth objectives.
13. Legal Protection
Reduce legal liabilities by identifying and addressing vulnerabilities that could lead to data breaches and subsequent legal actions.
14. Innovation Enablement
Remove security roadblocks, enabling teams to focus on innovation and business growth.
15. Data Protection
Safeguard sensitive data, preserve customer privacy, and maintain the integrity of proprietary information.
16. Board Confidence
Provide boards and stakeholders with evidence of a proactive security approach, enhancing confidence in the organization’s stability.
Advanced Tools & Techniques Deployed in Posture Assessment
Accorian employs tools and resources for efficient posture assessments and accurate reporting. This includes the use of Excel Spreadsheets, as well as an in-house tool called GoRICO. These tools streamline the assessment process, enabling us to provide clients with precise and insightful reports to enhance their cybersecurity posture.
Advanced Tools & Techniques Deployed in Posture Assessment
Accorian employs tools and resources for efficient posture assessments and accurate reporting. This includes the use of Excel Spreadsheets, as well as an in-house tool called GoRICO. These tools streamline the assessment process, enabling us to provide clients with precise and insightful reports to enhance their cybersecurity posture.
How Does Our Posture Assessment Assist
You In Meeting Compliance Requirements?
Accorian will play an integral role throughout the cybersecurity posture assessment process, assisting your organization in demonstrating its dedication to meeting compliance requirements and strengthening its overall security posture. Success in achieving assessment objectives hinges on Collaboration, Transparency, and a Proactive Approach.
- Gathering relevant documentation
- Engaging external experts (if required)
- Reviewing current security practices
- Conducting pre-assessment gap analysis
- Preparing technical documentation
- Scheduling the assessment with critical stakeholders
- Reviewing the findings and furnishing appropriate recommendations
- Developing a remediation plan and advisory in implementing the remediation actions
- Continuously monitor your security posture and conduct periodic assessments to ensure ongoing compliance (if required)
The Accorian Advantage
Accorian has a proven track record, having completed 400+ compliance consulting engagements across a broad spectrum of standards and regulations, including HITRUST, HIPAA, ISO 27001, SOC 2, NIST CSF, and GDPR, along with numerous penetration testing projects. Furthermore, we offer valuable services such as vCISO (Virtual Chief Information Security Officer) and vSecurity Team Services to provide organizations with effective cybersecurity management.
Our compliance team brings a wealth of experience, with each member boasting over 10+ years of expertise in cybersecurity and technology. This extensive collective experience empowers us to deliver comprehensive and efficient solutions that cater to our client’s cybersecurity and compliance needs. Our team holds a range of certifications, including CISSP, CEH, GWAPT, CISA, CRISC, BS 25999, HITRUST CCSFP, ISO 27001 LI & LA, PCI DSS QSA, and C|CISO, further solidifying our commitment to excellence and proficiency in the field.
CONSULTING & ASSESSMENT SERVICES
Office Address
Accorian Head Office
6,Alvin Ct, East Brunswick, NJ 08816 USA
Accorian Canada
Toronto
Accorian India
Ground Floor,11, Brigade Terraces, Cambridge Rd, Halasuru, Udani Layout, Bengaluru, Karnataka 560008, India
Ready to Start?
Wordpress Developer (3-5 Years)
Senior Manager - Penetration Testing (5-7 years)
Senior Manager - Compliance (5-7 Years)
Security Team Lead / Sr. Security Consultant (3-5 Years)
Security Consultant (1-3 Years)
Project Manager (2 - 4 Years)
Penetration Tester Consultant (2-4 years)
Lead Software Architect (10 years as a software developer, 3 years as a technical architect)
IT Analyst (1-2 Years)
Developer (3-5 Years)
Content Strategist & Editor (2-4 Years)
Role Summary:
As a wordpress developer, you would be responsible for the development, maintenance, and optimization of our company’s website. This role requires a strong understanding of web development technologies, content management systems, and a keen eye for design and user experience. You will play a crucial role in enhancing our online presence and ensuring a seamless user experience for our audience.
Mandatory Skill Sets/Expertise:
- Strong knowledge of web design principles and user experience best practices.
- Proficiency in web development languages (e.g., HTML, PHP, CSS, JavaScript)
- Proficiency in content management systems (e.g., WordPress, Drupal).
- Experience in managing Security tools – AV, MDM & DLP
Key Attributes:
- Proven experience in web development and content management.
- Familiarity with SEO strategies and tools.
- Excellent problem-solving skills and attention to detail.
- Strong communication and collaboration abilities.
- Ability to adapt to evolving web technologies and industry trends.
Key Responsibilities:
- Website development – Plan and execute website development projects. Develop and implement new website features, pages, and functionalities. Optimize user experience, including site navigation, page loading speed, and overall usability.
- In-depth expertise in WordPress – Demonstrate expertise in developing and customizing WordPress themes, plugins, and templates. The candidates should be proficient in PHP, HTML, CSS, and JavaScript, and have hands-on experience with popular WordPress frameworks and libraries.
- Multisite Management – Strong experience in efficiently managing WordPress multisite networks, including setup, configuration, maintenance, ensuring their stability and optimal performance. Implement A/B testing and gather user feedback to make data-driven improvements.
- Security and Maintenance – Ensure the security and integrity of WordPress installations by implementing best practices and staying updated with the latest security trends. Perform regular maintenance tasks to keep websites up-to-date and running smoothly.
- Server Management – Having hands-on experience in managing the Codes. Regularly update and maintain website content, including text, images, and multimedia elements
A day in the life
- Perform Penetration Testing for networks (internal & external), applications, APIs & cloud assets
along with Red & Purple Team assessments - Vulnerability identification and analysis
- Collaborate with team members and stakeholders to define project scopes, review test results,
and determine remediation steps - Draft reports and communicate complex security concepts and test findings to clients and
stakeholders - Make expert recommendations to help clients improve their information security program
- Work on researching & developing utilities, toolkits, processes, tactics, and techniques
Qualifications & Requirements
- 5-7 years of penetration testing experience, preferably in highly regulated industries and for
global clients - At least 2-3 years of experience in managing a team is a plus
- Proficiency with scripting and programming languages
- Advanced problem-solving skills
- OSCP/OSWE certification preferred but, GPEN, GWAPT, GXPN, CREST, CESG, and similar
certifications are a plus - Experience with Cobalt Strike a plus
- Strong written and verbal communication skills
- Ability to work autonomously with little directional oversight
- Ability to lead a project and multiple testers
- Commitment to quality and on-schedule delivery; and a proven ability to establish and meet
milestones and deadlines - Customer-focused mentality to understand and appropriately respond to customers’ business
needs
Role Summary
The senior manager is responsible for leading and sustaining the team that drives the compliance strategy by working collaboratively with internal teams, SMEs, external customers, vendors, auditors and other stakeholders. He/she should be able to work collaboratively with other departments and stakeholders to achieve company-wide goals and satisfy the client.
Mandatory Skill Sets/Expertise
- Relevant bachelor’s or master’s degree in computer science/ IT Auditing/ Information Systems/ Privacy.
- Have at least 5-7 years of relevant information security auditing experience and advanced knowledge of general controls (security, change management, disaster backup recovery, data centre, infrastructure, etc.), IT governance processes (ITIL).
- Ability to critically review security policies and procedures, design and implementation of security policies, procedures, standards and controls in line with regulation and/or current standards.
- Good understanding and implementation expertise of industry standards in cybersecurity (ISO, ITIL, NIST, ISF, SOC, HITRUST, PCI DSS, HIPAA) and privacy (GDPR, ISO 27018) is an advantage.
- Good project management skills with the ability to collaborate with teams across multiple locations and a strong command of the English language.
- Relevant industry recognized certifications such as CISSP/CISA/CISM.
Key Attributes
- Leadership: To lead by example, collaborate with the team, and make appropriate decisions when required. effectively communicate the vision and goals of the Accorian.
- Mentoring: To mentor individuals from graduate to industry qualified, with the aim of motivating and enhancing their personal and professional development.
- Communication: To communicate effectively both verbally and in writing, with the team and clients, sharing information in a clear and concise manner.
- Problem-solving: Strong analytical skills to identify and solve complex problems within the GRC domain.
Key Responsibilities
- Setting strategic direction for audit readiness, managing compliance programs, driving continuous improvement activities, & reporting metrics.
- Interfacing with stakeholders, articulating control implementation and impact, and establishing considerations for applying security and compliance concepts to a technical cloud environment.
- Effectively communicating compliance program results, including assessment status, workflow, remediation, and reporting, to a broad audience including peers, senior and executive leaders.
- Leading small teams by assigning and tracking individual tasks and ensuring the team meets milestones and addresses challenges.
- Coordinating the overarching annual audit plan with internal and external auditors to support delivery of multiple, simultaneous audits and certifications.
- Supporting delivery of audit milestones to ensure audit timelines stay on target by proactively identifying and coordination resolution of roadblocks.
- Collaborating cross-functionally with technology and business stakeholders to drive, track, and resolve all aspects of compliance readiness and audit execution
Role Summary:
The Sr. Security Consultant / Team Leader is responsible for leading a team of Security Consultants, managing team and professional development goals, ensuring on-time delivery of GRC projects, and providing expert guidance to team members on GRC-related matters.
Mandatory Skill Sets/Expertise
- Relevant bachelor’s or master’s degree in computer science/ IT Auditing/ Information Systems/ Privacy.
- Have a minimum of 3-5 years of experience in the domain of cybersecurity and privacy.
- Experience in information security standards and best practices (ISO 27001, SOC 2, NIST, HIPAA, PCI DSS, HITRUST, etc).
- Experience in performing assessments and audits.
- Deep understanding of risk management principles and IT controls.
- Certified in relevant and industry recognized certifications.
Key Attributes:
- Leadership: To lead by example, collaborate with the team, and make appropriate decisions when required. effectively communicate the vision and goals of the Accorian.
- Mentoring: To mentor individuals from graduate to industry qualified, with the aim of motivating and enhancing their personal and professional development.
- Communication: To communicate effectively both verbally and in writing, with the team and clients, sharing information in a clear and concise manner.
- Problem-solving: Strong analytical skills to identify and solve complex problems within the GRC domain.
Key Responsibilities:
- Assessing cybersecurity risks and vulnerabilities and partnering with the security team to identify and analyze potential threats, evaluating their impact and likelihood of occurrence.
- Developing and implementing GRC strategies to analyze industry regulations and standards relevant to cybersecurity, translating them into practical policies and procedures for our organization.
- End to End Implementation of various standards, regulatory and compliance requirements such as SOC 2, HIPAA, HITRUST, NIST CSF, ISO 27001.
- Conducting GRC audits and collaborating and performing regular evaluations of our security controls and compliance measures, identifying gaps, and recommending improvements.
- Collaborating with strategic-integration and fostering strong relationships across various departments (IT, security, legal, compliance) to ensure seamless integration of GRC processes and cybersecurity initiatives.
- Provide expert advice on GRC strategies, frameworks, and methodologies to clients.
- Collaborate with internal and external auditors, providing necessary documentation and support for audits.
- Ensure clients’ adherence to relevant regulations, standards, and industry-specific compliance requirements.
- Developing and delivering training programs to educate employees on cybersecurity best practices and compliance requirements, promoting a culture of security awareness.
- Staying informed on emerging threats and regulations and continuously update your knowledge on the evolving cybersecurity landscape and adapt your strategies accordingly.
- Coordinating the overarching annual audit plan with internal and external auditors to support delivery of multiple, simultaneous audits and certifications.
- Supporting delivery of audit milestones to ensure audit timelines stay on target by proactively identifying and coordination resolution of roadblocks
Role Summary
Accorian is actively seeking for a dynamic and seasoned Consultant/Senior Consultant specializing in
the Governance, Risk, and Compliance (GRC) domain to join our team. The preferred candidate will
assume a pivotal role in providing strategic guidance to clients regarding the implementation of sound
risk management practices overseeing vendor relationships, conducting audits across various
frameworks, and harnessing the capabilities of the GRC tool. This multifaceted position necessitates a
profound comprehension of GRC principles, regulatory compliance, and the ability to implement
resilient risk management strategies. Collaborate extensively with cross-functional teams, conduct
evaluations of organizational processes, and deliver strategic recommendations aimed at enhancing
GRC frameworks.
Mandatory Skill Sets/Expertise
1. Bachelor’s or master’s degree in computer science, Information Security, Risk Management,
Cyberlaw, or a related field.
2. Proficient in leading GRC frameworks and methodologies (SOC, ISO 27001, HIPPA, NIST, PCI DSS,
etc.).
3. Strong understanding of cybersecurity frameworks and principles (e.g., NIST Cybersecurity
Framework, ISO 27001, HIPAA).
4. Familiarity with audit processes, internal controls, and assurance methodologies.
5. Experience with GRC software solutions (e.g. SAP GRC, ACL, Archer, etc.).
6. Knowledge of risk assessment, control design, and reporting methodologies
7. Ability to work independently and as part of a team.
Preferred Certifications: CISSP, ISO 27001 Lead Auditor or Implementer.
Key Attributes:
a. 1 – 3 years of experience in consulting or industry roles related to GRC.
b. Proven track record of successful GRC program implementation and optimization.
c. Customer-centric mindset with a focus on understanding and addressing clients’ unique needs.
d. Ability to translate complex technical concepts into clear and actionable insights for clients.
e. Passion for staying up to date on the latest trends and developments in GRC.
f. Strong work ethic and a commitment to delivering high-quality results.
g. Add on Strong project management skills to successfully lead and execute projects.
Key Responsibilities:
1. Assessing cybersecurity risks and vulnerabilities and partnering with the security team to identify
and analyze potential threats, evaluating their impact and likelihood of occurrence.
2. Developing and implementing GRC strategies to analyze industry regulations and standards
relevant to cybersecurity, translating them into practical policies and procedures for our
organization.
3. Conducting GRC audits and collaborating and performing regular evaluations of our security
controls and compliance measures, identifying gaps, and recommending improvements.
4. Collaborating with strategic-integration and fostering strong relationships across various
departments (IT, security, legal, compliance) to ensure seamless integration of GRC processes and
cybersecurity initiatives.
5. Provide expert advice on GRC strategies, frameworks, and methodologies to clients.
6. Collaborate with internal and external auditors, providing necessary documentation and support
for audits.
7. Ensure clients’ adherence to relevant regulations, standards, and industry-specific compliance
requirements.
8. Developing and delivering training programs to educate employees on cybersecurity best
practices and compliance requirements, promoting a culture of security awareness.
9. Staying informed on emerging threats and regulations and continuously update your knowledge
on the evolving cybersecurity landscape and adapt your strategies accordingly
Role Summary
The role of the Project Manager would be to help plan and track cybersecurity & technology projects to meet KRAs, milestones & deadlines. This would also include coordinating. meetings with clients & internal teams and resource planning. The primary KRA would be to ensure projects are delivered on a timely manner and all stakeholders. are updated about the latest status of the project.
Mandatory Skill Sets/Expertise
- Great communication skills – written & oral
- At least 2 to 4 years of project coordination & management experience for technology consulting or implementation services.
- Strong planning, organizing, and execution skills
- Ability to work collaboratively with global teams & clients, and with staff of different backgrounds and experience levels along with managing goals.
- Strong interest in learning and developing professional skills
- Logical problem-solving skills; looks beyond immediate problems to consider root causes and addresses them.
- Possess a high degree of personal responsibility.
- Must have completed graduation.
Key Attributes
- Excellent communication skills
- Strategic thinking and visioning
- Excellent attention to detail
Key Responsibilities: –
- Provide support and assistance to the program and aid by tracking.
- Completion of all required tasks to meet project and client goals.
- Foresee; manage; and raise appropriate visibility to risks and issues.
- Drive resolution of any conflicts and escalate as needed to avoid roadblocks.
- Drive execution rigor using set practices; Manage & Drive Change wherever needed.
- Generate and publish weekly reports; corporate process improvements in developing new reports.
- Organizing, attending, and participating in stakeholder meetings.
- Documenting and following up on important actions and decisions from meetings.
- Developing project strategies
- Ensuring projects adhere to our clients’ frameworks and all documentation is maintained. appropriately for each project
- Ensure stakeholder views are managed towards the best solution.
- Chair and facilitate meetings where appropriate; distribute minutes to all project team.
- Track deliverables and calendar timelines
A day in the life
- Perform Penetration Testing for networks (internal & external), applications, APIs & cloud assets along with Red & Purple
Team assessments - Vulnerability identification and analysis
- Collaborate with team members and stakeholders to define project scopes, review test results,
and determine remediation steps - Draft reports and communicate complex security concepts and test findings to clients and
stakeholders - Make expert recommendations to help clients improve their information security program
- Work on researching & developing utilities, toolkits, processes, tactics, and techniques
Qualifications & Requirements
- 2-4 years of penetration testing experience, preferably in highly regulated industries and for global clients
- Proficiency with scripting and programming languages
- Advanced problem-solving skills
- OSCP certification preferred but, GPEN, GWAPT, GXPN, CREST, CESG and similar certifications a plus
- Experience with Cobalt Strike a plus
- Strong written and verbal communication skills
- Ability to work autonomously with little directional oversight
- Ability to lead a project and multiple testers
- Commitment to quality and on-schedule delivery; and a proven ability to establish and meet milestones and deadlines
- Customer-focused mentality to understand and appropriately respond to customers’ business needs
Role Summary:
As the Lead Software Architect, you will be a key leader in the development and evolution of our B2B SaaS product & it’s associated systems. The entire development team will report to you.
Drawing upon your extensive technical expertise and industry knowledge, you will design and implement scalable, robust, and efficient software solutions. Collaboration with cross-functional teams, technical leadership, and staying abreast of emerging technologies will be essential for success in this role.
About Our Product:
GORICO was incepted by security practitioners & audits with decades of experience to simplify the security conundrum and streamline the security compliance and security maintenance process. Security is a growth enabler today as it’s table stakes for doing business and a mandatory requirement as part of the third-party risk strategy of clients.
This is a single solution tailored to an organization to manage all your security adherence, compliance, vendor risk, vulnerability management , policy & procedure management and risk assessment needs.
It enables behaviour change and shift in the mindset towards security. It’s the only way to address the current reactive approach to it. Hence, going from a once a year or, couple of times a year audit rush to year long sustenance of security.
Hence, GORICO empowers organizations to understand, attain and sustain true security.
Mandatory Skill Sets/Expertise
- Proven experience as a Software Architect, with a track record of successful project delivery. A minimum of 2-3 years in this role
- Proven experience of building a B2B SaaS/Enterprise product
- Should’ve managed a software development team
- Strong proficiency in software design principles, patterns, and architectural best practices
- Expertise in multiple programming languages and frameworks including Node.js, React.js, Express, PostGreSQL
- Experience in integrating with APIs, SaaS solutions, ETL platforms
- Experience with AWS
- In-depth knowledge of database design, cloud computing, and microservices architecture
- Excellent problem-solving and analytical skills
Key Attributes
- Strategic thinking and vision
- Strong leadership and communication skills
- Adaptability and willingness to learn new technologies
- Detail-oriented and committed to delivering high-quality solutions
- Ability to collaborate effectively in a team environment
Key Responsibilities
- Architectural Design & SDLC:
- Review existing architecture and oversee areas of improvement
- Lead the design and development of new features and enhancements
- Define and document high-level architecture, including system components, modules, and interactions
- Lead the entire SDLC lifecycle and be hands on as the lead for the development team
- Technical Leadership:
- Provide technical leadership and guidance to the development teams
- Mentor and coach team members, fostering a culture of innovation and excellence
- System Integration:
- Collaborate with stakeholders, including the product manager, engineers, and internal teams, to ensure seamless integration of software components
- Design and implement interfaces and integration points between various system modules
- Scalability and Performance:
- Design scalable and high-performance software solutions that meet current and future business needs
- Conduct performance analysis and optimization to enhance system efficiency
- Technology Selection:
- Stay current with industry trends and emerging technologies
- Evaluate and recommend technologies, tools, and frameworks that align with business objectives
- Ability to substantiate and take build-vs-buy decisions
- Security and Compliance:
- Integrate security best practices into the software architecture
- Ensure compliance with relevant industry standards and regulations
- Code Review and Quality Assurance:
- Conduct code reviews to ensure adherence to architectural guidelines and best practices
- Assist QA team members to establish and maintain quality standards
- Documentation:
- Document architectural decisions, designs, and guidelines
- Prepare technical documentation for both internal and external audiences
- Feedback & Enhancement:
- Analyses market & user research to make data-driven decisions ▪ Implement feedback from clients
Role Summary:
As an IT Engineer, you will play a pivotal role in providing technical support to our internal members and ensuring the smooth operation of our IT environment. You will work under the guidance of IT Manager to resolve technical issues, help end-users, and contribute to the overall success of our IT support team
Mandatory Skill Sets/Expertise
- 1-2 years’ experience in IT Support or a related role
- Strong knowledge of Windows and/or Mac operating systems
- Proficiency in troubleshooting hardware and software issues
- Familiarity with network configurations and protocols
- Certifications such as CompTIA A+ or Microsoft Certified Desktop Support Technician (MCDST) is a plus
- Willingness to learn and adapt to new technologies and methodologies
- Strong problem-solving and analytical skills Key Attributes
- Good communication and customer service skills
- Adaptability and willingness to learn new technologies
- Detail-oriented and committed to delivering high-quality solutions
- Ability to collaborate effectively in a team environment
Key Responsibilities
- Provide first-level technical support to end-users, both remotely and on-site
- Assist with the installation, configuration, and maintenance of hardware and software
- Troubleshoot and resolve hardware/software issues in a timely manner
- Monitor and respond to IT service requests and incidents
- Maintain accurate and up-to-date records of Assets, support requests, incidents, and resolutions
- Assist with user account management and access control
- Ensure IT security and compliance measures are adhered to
- Participate in IT projects, such as system upgrades and deployments
- Assist in creating and updating IT documentation and knowledge base articles
- Stay up to date with the latest technology trends and best practice
Role Summary
As a developer, you will be responsible for designing, coding, testing, modifying and implementing new features in the B2B SaaS product. You would closely work with the technical architect towards building a scalable GRC tool.
Mandatory Skill Sets/Expertise
- Proven experience as a developer, with a track record of building scalable B2B SaaS/Enterprise product
- Strong coding skills in Node.js, React.js, Express, PostGreSQL
- Expertise in multiple programming languages and frameworks including
- Experience in integrating with APIs, SaaS solutions, ETL platforms
- Experience with AWS
- In-depth knowledge of database design, cloud computing, and microservices architecture
- Excellent problem-solving and analytical skills
Key Attributes
- Excellent coding skills
- Good communication skills
- Strong analytical and problem-solving skills
- Adaptability and willingness to learn new technologies
- Detail-oriented and committed to delivering high-quality solutions
- Ability to collaborate effectively in a team environment
Key Responsibilities
- Experience in developing B2B SaaS /Enterprise products using Node Js and React Js
- Manage code deployments, fixe, updates and other related processes
- Produce scalable code as per product and business requirement
- Troubleshooting, debugging, maintaining and improving the existing product
- Responsible for developing technical documentation to guide future product development
- Conduct performance analysis and optimization to enhance system efficiency
Role Summary
As a Content Strategist & Editor, you would be responsible for strategizing and creating high quality, engaging and informative content including blog spots, articles, product/service descriptions and other forms of digital and print media. You would be responsible for enhancing the brand awareness of Accorian whereby contributing towards lead generation from prospective customers.
Mandatory Skill Sets/Expertise
- Master of spelling, grammar, and punctuation
- Holds a keen interest in reading and has a high level of comprehension
- Thorough grasp of the English language with advanced vocabulary and grammar
- Ability to summarize information without losing the original meaning
- Understand trending technological and business concepts correctly, write compelling copy for popular concepts
- Proficiency with software/applications such as Microsoft Word, Excel, PowerPoint
- Experience working in a start-up environment
- Ability to actively participate in the adoption of digital tools and strategies
- Preferred experience – creation of knowledge library
- Ability to bring in language and content standardization in presentations, documentation, and reports.
- Ability to work on multiple projects with different objectives simultaneously Key Attributes
- Excellent communication skills (written as well as verbal)
- Excellent attention to detail
- Business acumen
Key Responsibilities
- Conduct extensive research and interviews to ensure content is accurate and up-to-date
- Engage readers with an informative, entertaining, and educational copy
- Understand and consistently reflect the branding of the company
- Work closely with internal stakeholders and external subject matter experts to develop content
- Proofread to standardize existing documents and edit at various stages of the writing process in response to feedback from internal management
- Conduct spot checks to evaluate quality of work
- Resolve queries, especially those related to language and style
- Should be able to give eye-catchy headlines and provide keywords on a regular basis
- Coordinating and contributing to proposal production while working collaboratively with other team members
- Work on presentations by evaluating texts and graphics
- Performing plagiarism checks
- Review of text/content going on various social media platforms of Accorian
Drop your CVs to joinourteam@accorian.com
Interested Position
