In the dynamic healthcare landscape, where innovation meets responsibility, safeguarding sensitive data is paramount. The stark reality is that our data is consistently under siege. In 2023, the healthcare sector witnessed a staggering 60% surge in data breaches, inflicting an average financial cost of $10.93 million per breach. This financial impact necessitates urgent action, emphasizing the need to fortify defenses and embrace cyber hygiene practices like HITRUST certification.
WHAT IS HITRUST CERTIFICATION?
HITRUST was established in 2007 to address security and privacy concerns regarding sensitive information. At its core lies the Common Security Framework (CSF), a standard in healthcare data protection that validates an organization’s adherence to stringent healthcare data protection standards. The HITRUST CSF is designed for organizations that create, access, store, or share sensitive data.
Achieving HITRUST certification demands meticulous implementation of necessary controls in the designated environment. Voluntary yet pivotal, HITRUST aids businesses in aligning with mandatory regulations such as HIPAA, PCI DSS, and ISO 27001, making it a proactive framework for organizations navigating the complex terrain of data security.
STEPS TO GET HITRUST CERTIFIED
- Readiness Assessment
- Define the scope of work for HITRUST
- Use the HITRUST MYCSF® tool to understand several controls under consideration
- At a high level, review the HITRUST domains and identify gaps in comparison to the current state
- Create a roadmap plan towards certification
2. Roadmap Execution
- Partner with the client to implement a roadmap
- Assist in creating policies/procedures
- Perform security testing
- Assist with program management
3. Incubation
- HITRUST is a maturity model
- HITRUST requires organizations to demonstrate implementation of their policies and procedures for at least 90 days prior to initiating the Validated Assessment
4. Validated Assessment
- Audit the evidence uploaded to MYCSF® by the client
- Test against control requirements, comment, and score each control
- Partner with the client to mitigate gaps and implement proper procedures
- Submit Validated Assessment to HITRUST for Validation/Certification to HITRUST
5. Maintaining HITRUST Certification
- For an e1, annual Validated Assessment
- For an i1, rapid recertification in the second year
- For an r2, an interim assessment in the second year
TYPES OF HITRUST ASSESSMENTS
1. HITRUST e1 Assessment
HITRUST e1 Assessment is a foundational cybersecurity framework. It is an excellent starting point for organizations to get oriented with the HITRUST CSF framework.
2. HITRUST i1 Assessment
HITRUST i1 Assessment is designed for healthcare organizations and business partners who require moderate assurance.
3. HITRUST r2 Assessment
HITRUST r2 assessment is globally recognized as a high-level validation showing that an enterprise successfully manages risk by meeting and exceeding industry-defined standards for cybersecurity.
BENEFITS OF BEING HITRUST CERTIFIED
1. Table Stakes
Companies must adhere to strong information security practices to become healthcare industry leaders. Among the various security credentials, HITRUST compliance stands out as the preferred choice sought by health clients. Achieving HITRUST certification increases the opportunities for organizations to expand their TAM (Total Addressable Market) and enhances their revenue potential.
2. Recognized as the Gold Standard
According to research conducted by HITRUST, organizations that pursue HITRUST CSF certification witness remarkable improvements in their information security posture, with an impressive 97% of organizations successfully achieving and sustaining a robust security posture.
3. Reduces the risk of Cyber Attack and Data Protection
HITRUST CSF Certification contributes to the robust security of health data, intellectual property, and other proprietary information, bolstering data security and mitigating data breaches.
4. Shorter Future Audits
HITRUST’s robustness and comprehensive approach make achieving secondary security standards easier through established policies and controls.
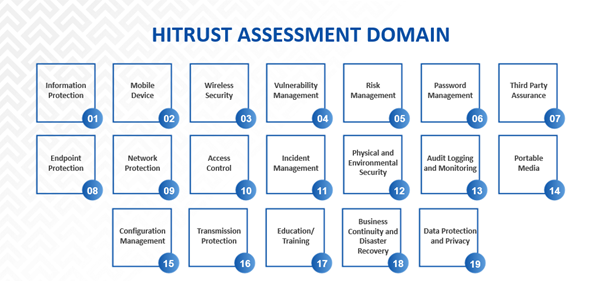
HITRUST ASSESSMENT DOMAIN
To achieve the HITRUST Certification requirement, an organization must achieve a minimum score of 63% in each domain, which only applies to r2, and for e1 & i1, the minimum score is 83%
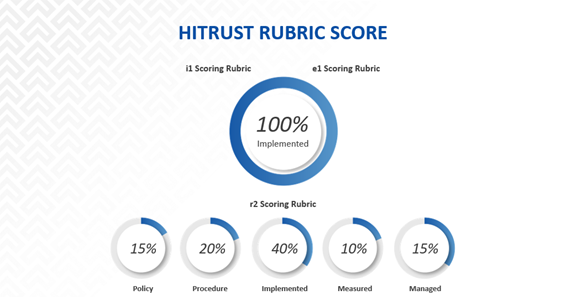
HITRUST RUBRIC SCORE
The HITRUST Control Maturity Scoring Rubric is a tool that evaluates the effectiveness of an organization’s information security and privacy program. It assigns a score to each control based on its maturity level. The score obtained through this rubric is a numerical or qualitative representation of how well an organization’s program aligns with the HITRUST framework.
Frequently Asked Questions (FAQ’s)
1. HOW MUCH DOES HITRUST CERTIFICATION COST?
The cost of a HITRUST Certification depends on the scope of the process and the assessment type. Additionally, costs are associated with purchasing the Validated HITRUST report and undergoing the assessment process. Accorian can help get you started with successfully scoping for your assessment and facilitating the process to reduce the cost, time, and resources.
2. WHICH HITRUST ASSESSMENT IS BEST FOR MY ORGANIZATION?
Determining the appropriate HITRUST Assessment for your organization depends on several factors, with the primary consideration being the level of risk the organization is exposed to. If an organization has a lower risk, starting with an e1 or an i1 Assessment is recommended, while medium to high-risk organizations should opt for an r2 Assessment. Accorian can assist organizations in making this decision by working with your team to understand your goals, requirements, and contracts.
3. HOW LONG DOES IT TAKE TO GET HITRUST CERTIFIED?
The entire HITRUST process may take 9 – 14 months
- Readiness Assessment: 4- 5 weeks
- Roadmap Execution: 4 – 5 months
- Incubation: 3 months
- Validated Assessment: 3 months
- Maintenance: Ongoing
4. ARE INTERNAL EMPLOYEES INVOLVED IN THE PROCESS?
Yes, some of your internal employees will be called upon to assist. Members of the IT security team, operations infrastructure, administrative, and vendor management are all included.
5. WHERE CAN I FIND AN ASSESSOR?
To begin the Validated Assessment process, you must select an authorized HITRUST CSF Assessor. An authorized HITRUST CSF Assessor is a company approved by HITRUST to conduct assessments and offer other services related to the HITRUST CSF Assurance Program as well as the HITRUST CSF security and privacy framework.
After selecting an authorized HITRUST CSF assessor, you must purchase a Validated Assessment from HITRUST.
CHOOSE ACCORIAN AS YOUR HITRUST PARTNER
Achieving HITRUST CSF certification can be a challenging process. However, as an authorized HITRUST Assessor, Accorian specializes in assisting businesses of all sizes to achieve certification. Our security team possesses extensive experience in HITRUST implementation and certification, enabling us to serve as your full-service cybersecurity partner throughout the process. We work with you to reinforce your company’s compliance and ensure you meet all requirements for HITRUST certification.