Written By: Vignesh M R ||
Third-Party Risk Management is the process of analyzing and controlling the risks present in your organization that are caused by outsourcing to Third-Party Service Providers (TPSP). On Average, organizations spend over $10 million annually responding to third-party security breaches.
Importance of TPRM
As many firms choose to outsource certain functions to third-party providers, the dangers of exposure to sensitive information increase drastically. These statistics are based on reports and surveys that talk about organizations’ challenges with regard to Vendor Risk Management (VRM).
- 98% of firms had at least one third-party partner who suffered a breach in the last two years, and according to a report, on average, a firm maintained around 10 third-party relationships
- 40% of organizations surveyed experienced a cyber incident linked to a third party, and another 21% experienced multiple incidents
- 18% of risk and compliance professionals identified third-party ethics or compliance failures as one of the root causes of compliance issues their businesses experienced over the past three years
- 59% of senior decision-makers view using third parties as the most significant corruption risk facing their organization
- 64% of organizations stated that their boards of directors and executive teams view Third-Party Risk Management as strategically imperative
- 72% of compliance and risk professionals agreed that their third-party due diligence program significantly reduced their legal, financial, and reputational risks
- 54% of organizations reported experiencing a data breach caused by one of their third parties in the last 12 months
- 31% of risk executives said third-party risk presented the greatest threat to their company’s ability to drive growth
Sources – Cyentia Institute and Security Scorecard Research Report 2023, Unity and CyberGRX 2023, Navex Global’s Definitive Risk & Compliance Benchmark Report 2023, Global Compliance Risk Benchmarking Survey 2023, Data Risk in the Third-party Ecosystem Study 2022, and PwC Pulse Survey of CROs and Risk Management Leaders 2022.
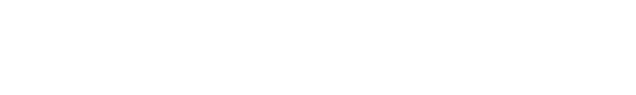
Correlation Between Organization Size and Compliance Status
Compliance Status Based on Organization Size
By leveraging TPRM due diligence data from different sources, we can effectively segment vendors into three categories based on their organizational size: Small, Medium, and Large. This methodological approach enhances the reader’s trust in the data. Here is how organizations are categorized based on their size:
- Small = 1 – 500
- Medium = 1K -5K
- Large = 5K – 10K
The following data represents the compliance status of vendors based on the size of the organization: small, medium, and large.
Compliance Status Based On Organization Size
The following data illustrates the average compliance status across organizations, independent of their size.
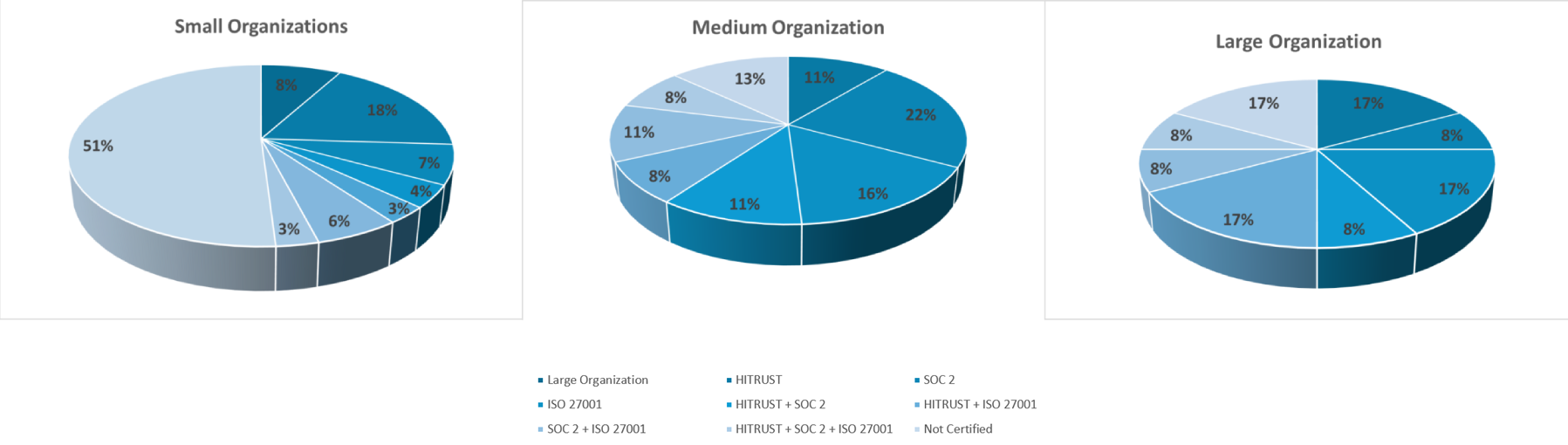
Volume of Questionnaires Based on Vendor Criticality Level
Third-party Risk Management programs categorize vendors based on the criticality levels of their services. This often determines the level of review, and the number of questions posed during the assessment process, which can vary depending on the vendor’s criticality level.
Factors Influencing the Number of Questions
- Industry Standards: Different industries have varying standards and regulatory requirements, influencing the number of questions. For example, the healthcare and finance industries typically have more stringent requirements
- Risk Appetite of the Organization: Organizations with a lower risk appetite might pose more questions to ensure thorough risk mitigation
- Vendor Relationship: The nature of the vendor relationship also influences the number of questions. For example, a long-term strategic partner vs. a short-term service provider can affect the depth of the assessment
Note: These numbers are indicative and can vary based on specific TPRM frameworks and organizational requirements.
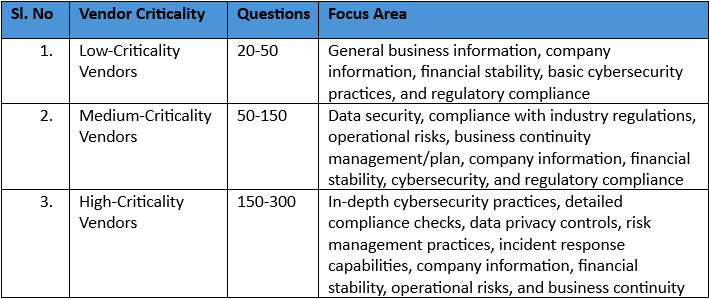
Average Number of Questions per Questionnaire by Industry Type
The average number of questions posed to vendors in a Third-party Risk Management program can vary based on the criticality of the vendor and the specific industry. Here’s a breakdown of typical question counts by vendor criticality and industry type:
Note: These averages can vary based on specific organizational requirements, risk appetite, and regulatory environment. The numbers provided offer a general guideline and can be adjusted according to the specific context and needs of your organization’s TPRM program.
Source: Google
Most Recommended Certifications for Your Organization
The most recommended certifications to manage your organization’s third-party risks are SOC 2 and ISO 27001. The ideal certification for your organization depends on various factors like:
- Maturity level
- Regulatory Requirements
- Global reach
- Resource availability
While using either ISO 27001 or SOC 2 can significantly improve your information security posture, there can be advantages to implementing both:
Comprehensive Coverage
- ISO 27001 provides a broad framework for information security management
- SOC 2 addresses specific trust service criteria (security, availability, processing integrity, confidentiality, and privacy)
Deeper Controls
- ISO 27001 requires a documented Information Security Management System (ISMS) with detailed controls for handling information risks
- SOC 2 frames this by verifying the effectiveness of those controls through an independent audit
Global Recognition
- ISO 27001 is an internationally recognized standard for information security best practices
- SOC 2 is widely accepted in North America and progressively valued globally, building trust with a broader audience
Transparency and Assurance: Both certifications involve independent audits, assuring stakeholders that information security is managed effectively. This clarity builds trust with clients, partners, and investors
Meeting Customer Demands: Organizations exclusively in highly regulated industries require sturdy information security practices from their vendors. Dual certification demonstrates a competitive edge
In conclusion, adopting a comprehensive and informed approach to cybersecurity assurances is mandatory in today’s intricate cyber threat landscape, especially within the healthcare industry, where the stakes are exceptionally high.
One key benefit of achieving SOC 2 attestation is the assurance it provides to clients. This certification signifies your organization has adequate controls for data protection, access management, incident management, business continuity, data protection, etc. This enhances trust and demonstrates your organization’s commitment to handling customers’ data, which is a crucial aspect for SaaS providers. It also represents your organization’s commitment to information security, particularly in a cloud environment.
Cost Benefit with TPRM
Outsourcing Third-Party Risk Management or vendor due diligence to Accorian can have significant implications for both cost and benefits. Here’s a detailed cost-benefit analysis to help you understand the financial and strategic impacts of such a decision:
Costs of Outsourcing TPRM or Vendor Due Diligence:
1. Direct Costs
- Service Fees: Accorian charges regular service or flat annual fees based on the number of vendors assessed.
- Consulting and Setup Costs: While there are initial costs for setting up the service, the potential for cost savings in the long run can be significant, including consulting, integration, and customization fees
2. Indirect Costs
- Internal Coordination: Internal teams must spend time and effort coordinating with the outsourced provider, including regular meetings, data sharing, and oversight
- Training: Train internal staff to work effectively with the outsourced provider, understand new processes, and manage transitions
- Potential Disruption: Temporary disruptions from in-house to outsourced services during the transition period
Outsourcing Benefits of TPRM/VRM
1. Direct Benefits
- Cost Savings: Your organizations can realize substantial savings on hiring, training, and maintaining an in-house TPRM team
- Access to Expertise: Leveraging the specialized knowledge and expertise of the outsourced provider can instill confidence in thorough and accurate risk assessments, providing a sense of security
2 Indirect Benefits
- Efficiency: Faster and more efficient vendor assessments due to the provider’s established processes and tools
- Focus on Core Business: Allowing internal teams to focus on core business activities and strategic initiatives rather than the detailed work of TPRM
- Scalability: Ability to easily scale the TPRM process as your organization grows or as the number of third-party relationships increases
3. Long-term Benefits
- Improved Risk Management: Enhanced risk management is achieved through continuous monitoring and expert assessment of third-party risks
- Regulatory Compliance: Ensuring compliance with regulatory requirements through professional management of vendor due diligence processes
- Enhanced Vendor Relationships: Potential for improved vendor relationships due to more consistent and professional risk management practices
Conclusion
Outsourcing TPRM or vendor due diligence can provide meaningful net benefits, particularly after the initial setup phase. The ongoing benefits of improved risk management, compliance, and operational efficiency cancel out the recurring costs, resulting in a positive return on investment. This strategic action can augment your organization’s ability to manage third-party risks effectively while allowing internal resources to focus on core business activities.
Note: Presenting this analysis to the client can help them decide whether the benefits of the TPRM services outweigh the costs.
FAQs on Third-party Risk Management
Here are some frequently asked questions about Third-Party Risk Management:
TPRM is essential because it mitigates risks associated with third-party vendors, protects sensitive data, and minimizes potential security breaches. Effective TPRM reduces financial and reputational damage, ensures compliance with regulations and maintains organizational integrity.
A vendor risk assessment questionnaire evaluates third-party vendors’ security practices, compliance, and operational risks. It helps organizations gauge potential risks associated with outsourcing and ensures vendors meet necessary standards and regulations.
A TPRM assessment evaluates and manages risks posed by third-party vendors. It involves analyzing vendors’ security, compliance, and operational practices to ensure they align with your organization’s risk management strategies and regulatory requirements.
Yes, the number of questions in the TPRM questionnaire typically changes based on the criticality level. Higher criticality levels usually involve more detailed and comprehensive questions to address more significant risks.
The primary advantages of third-party due diligence include mitigating risks, ensuring compliance, securing legal protection, safeguarding financial interests, protecting your reputation, and enhancing operational efficiency.